PAM manual¶
Introduction¶
Excalibur utilizes the mobile phone to act as a secure hardware token for any and all authentication and authorization inside of the Enterprise. Excalibur PAM (Privileged Access Management) provides web-based zero-trust access to Enterprise resources. Zero-trust means the client machine doesn’t need to be trusted as nothing is installed on it and all access from it goes via browser or native client utilizing a well-known protocol such as RDP. The client machine doesn’t get access to the internal network.
This manual describes how to use Excalibur PAM as well as PAM Management for users with admin privileges.
Prerequisites¶
To be able to use Excalibur PAM it is necessary to have:
- Registered account in Excalibur
- Modern web browser (Chrome is strongly preferred).
- Excalibur application on your smartphone, download from: https://getexcalibur.com (in the footer)
- Internet connectivity (page where runs excalibur server needs to be reachable).
Excalibur Dashboard - PAM¶
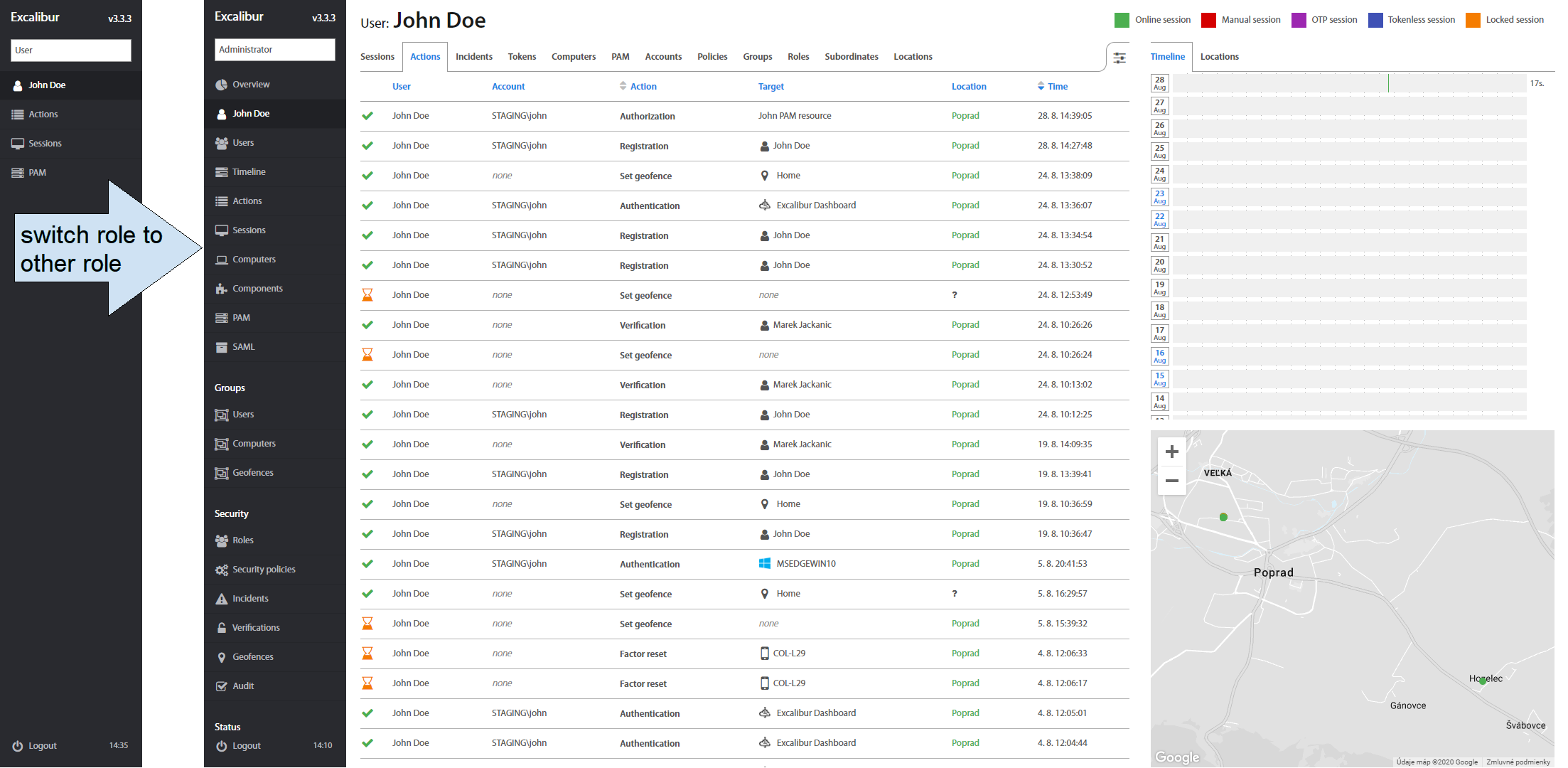
Excalibur Dashboard is the interface for users to access Enterprise resources allocated to them (via PAM), review their own activity, security policy which is assigned to them and manage their own temporary or home locations. Administrators have full access to all sections of Excalibur Dashboard and can use it to set up and manage all aspects of its functionality. More info about Excalibur Dashboard is available in the Excalibur Dashboard manuals. Brief description of sections visible to every user:
-
 Personal overview - contains information about user account, tokens and computers which the user uses as well as user’s activity and logged / recorded sessions.
Personal overview - contains information about user account, tokens and computers which the user uses as well as user’s activity and logged / recorded sessions. -
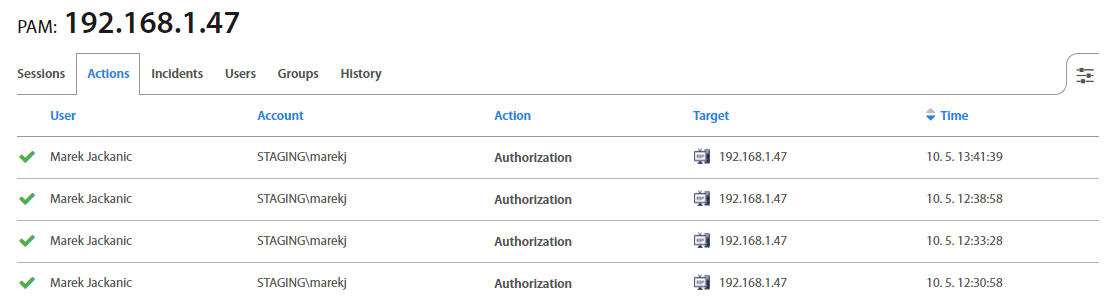
 Actions - list of all Actions taken by a user, such as Authentication, Authorization, Verification, Registration, Authentication, Factor reset, Tokenless, Authentication, Show Password and Set geofence.
Actions - list of all Actions taken by a user, such as Authentication, Authorization, Verification, Registration, Authentication, Factor reset, Tokenless, Authentication, Show Password and Set geofence. -
 Sessions - list of all Logged, Active, and Manual sessions, as well as their History.
Sessions - list of all Logged, Active, and Manual sessions, as well as their History. -
 PAM - provides web-based access to Enterprise resources – either directly acting as a HTML5 to other protocols proxy server (RDP, SSH, Telnet, VNC or even Browser access) or via dynamic port-forwarding that enables native clients such as RDP to access resources on the internal network via port forwarding on Excalibur PAM.
PAM - provides web-based access to Enterprise resources – either directly acting as a HTML5 to other protocols proxy server (RDP, SSH, Telnet, VNC or even Browser access) or via dynamic port-forwarding that enables native clients such as RDP to access resources on the internal network via port forwarding on Excalibur PAM.
Users may be able to switch between roles (if they have multiple roles) via a selector on top left corner of the UI.
Excalibur PAM considers all sessions “privileged” and by default recorded. Every action taken by the user is cryptographically signed to certify it was performed by the authenticated user. The effect of this is that there is continuous matching of every user action (as every user action and user PAM session is recorded and cryptographically signed) to strongly multi-factor authenticated identity. With no way to delegate access or claim it was some other user.
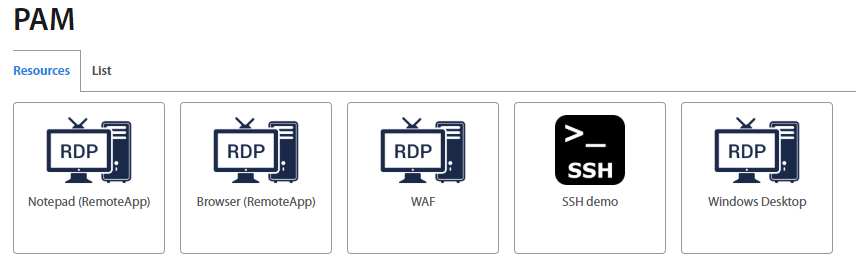
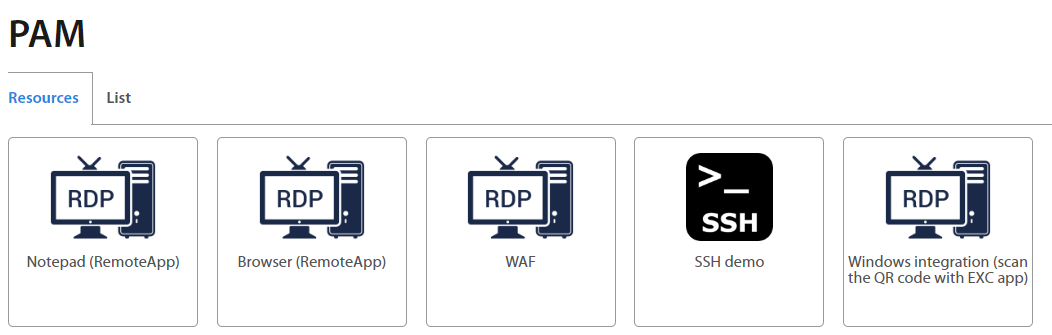
After successful login to Excalibur Dashboard, the default view is the User detail page. To display PAM resources click on PAM on the left menu. PAM page consists of the Resources and List tab, from where user can open assigned applications or review executed sessions. Administrator can create and manage PAM resources.
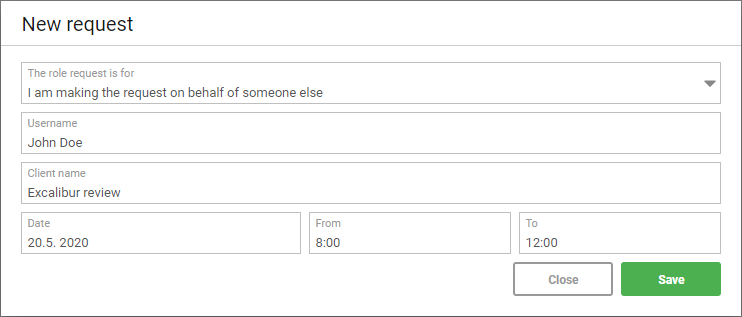
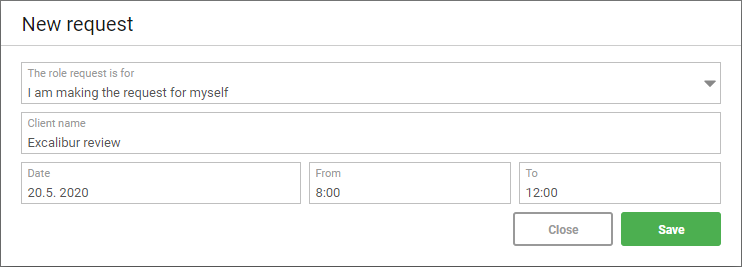
Users with elevated privileges can create temporary access to requested resources for users. The confirmation mail with instructions is sent to the user.
- Resources tab - shows all Applications which are assigned to the user's account. By clicking on the desired icon, the selected connection will be opened in a new tab.
- List tab - shows all assigned resources and their type. If user clicks on
 button, the connection will be established. By clicking on a specific application, further details will be shown (see section Application Details).
button, the connection will be established. By clicking on a specific application, further details will be shown (see section Application Details).
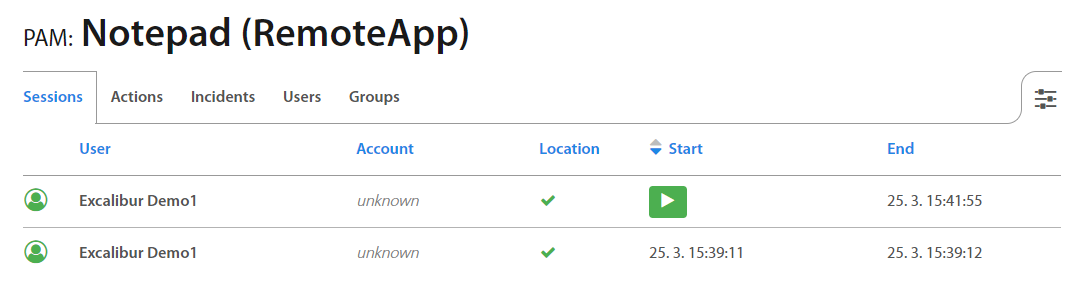
Application Details¶
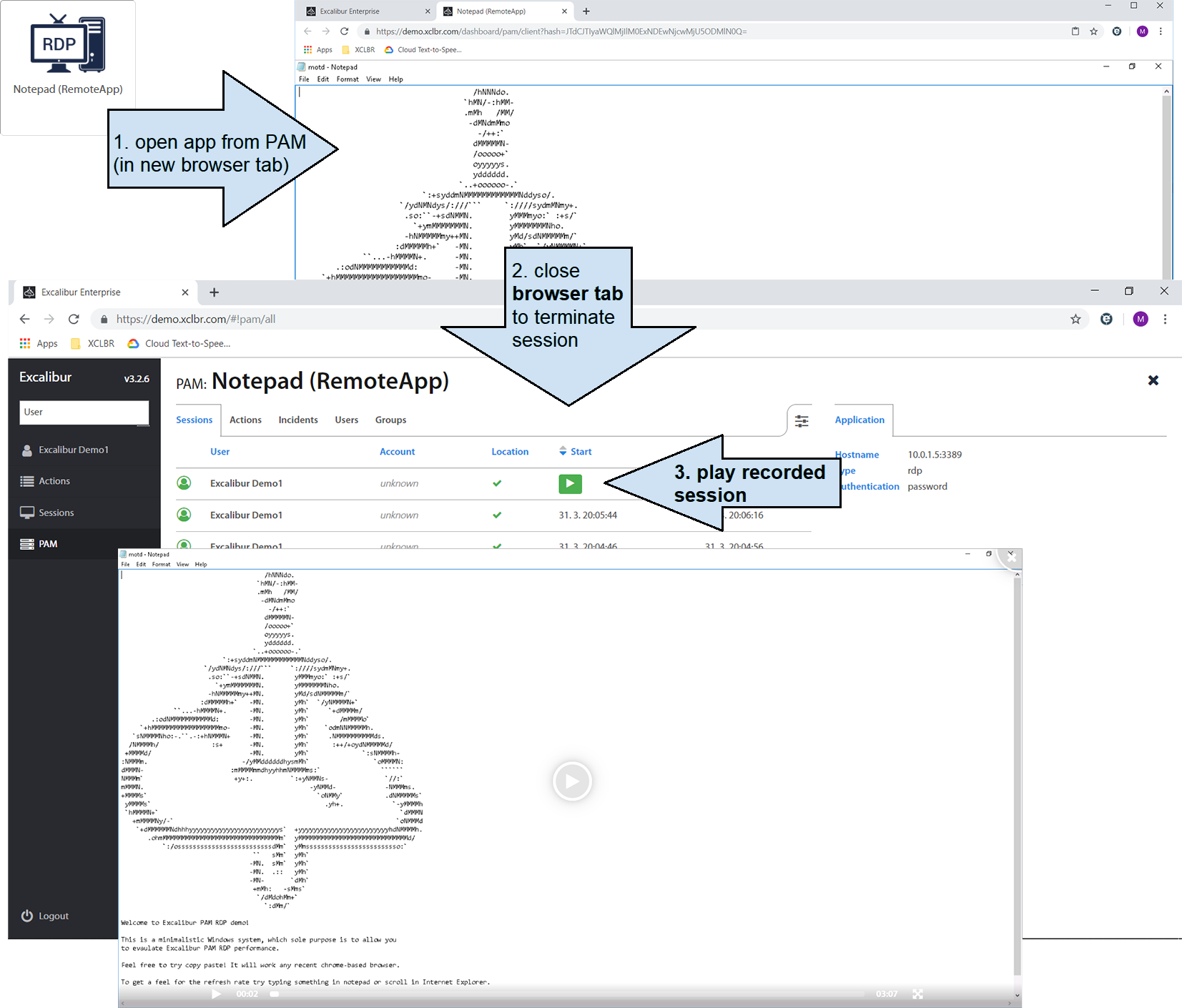
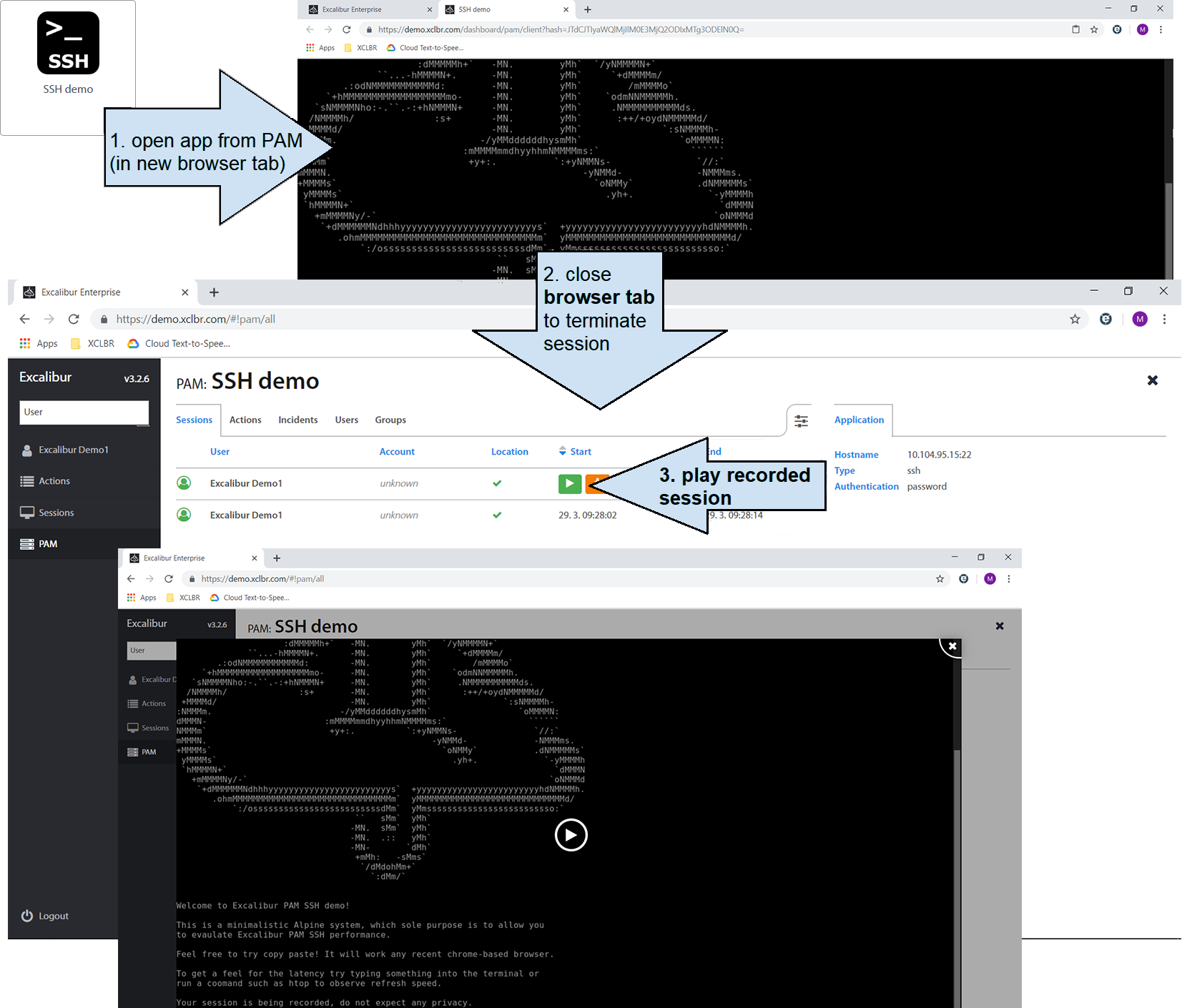
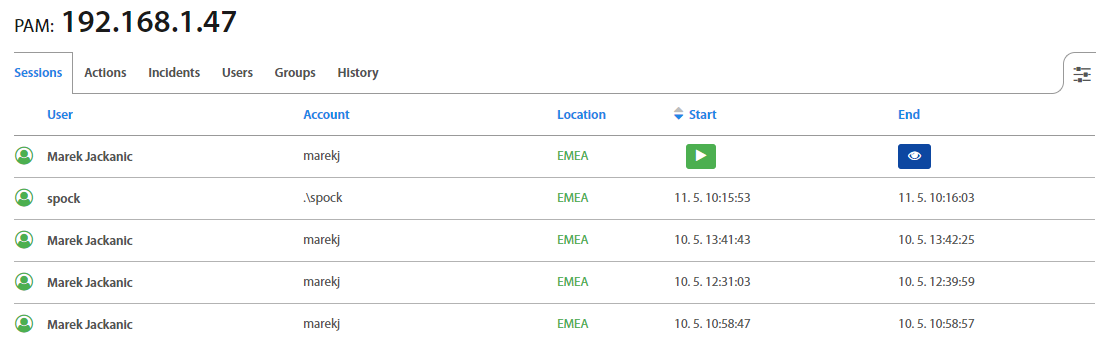
Sessions tab lists all the past and active user sessions as well as their start / end time.
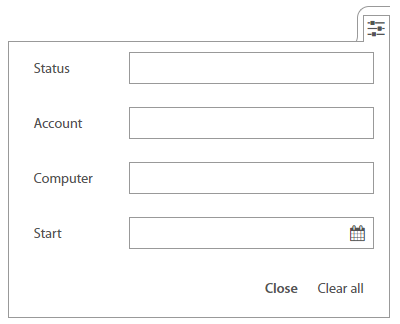
It’s also possible to filter Sessions by Account, Computer, Status or Start time in the top right corner.
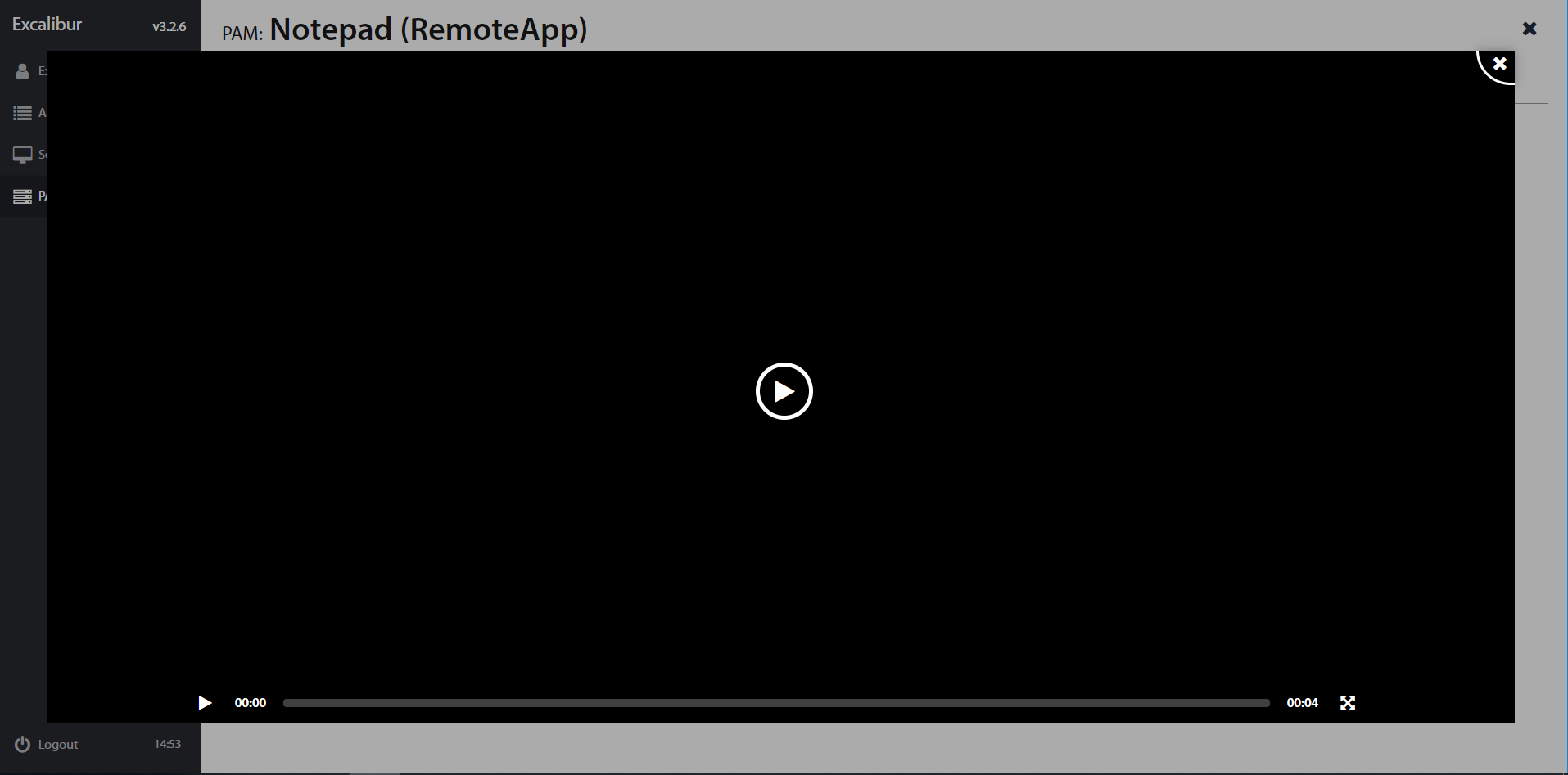
All PAM sessions are by default recorded. By hovering over specified session, the button shows up. Click on to play the session. For SSH connections, it is also possible to download typescript and typescript timing information by clicking on the or  button. Service Desk has not accesst to see recorded sessions.
button. Service Desk has not accesst to see recorded sessions.
Click on the button to play the recorded session using web browser.
RemoteApps¶
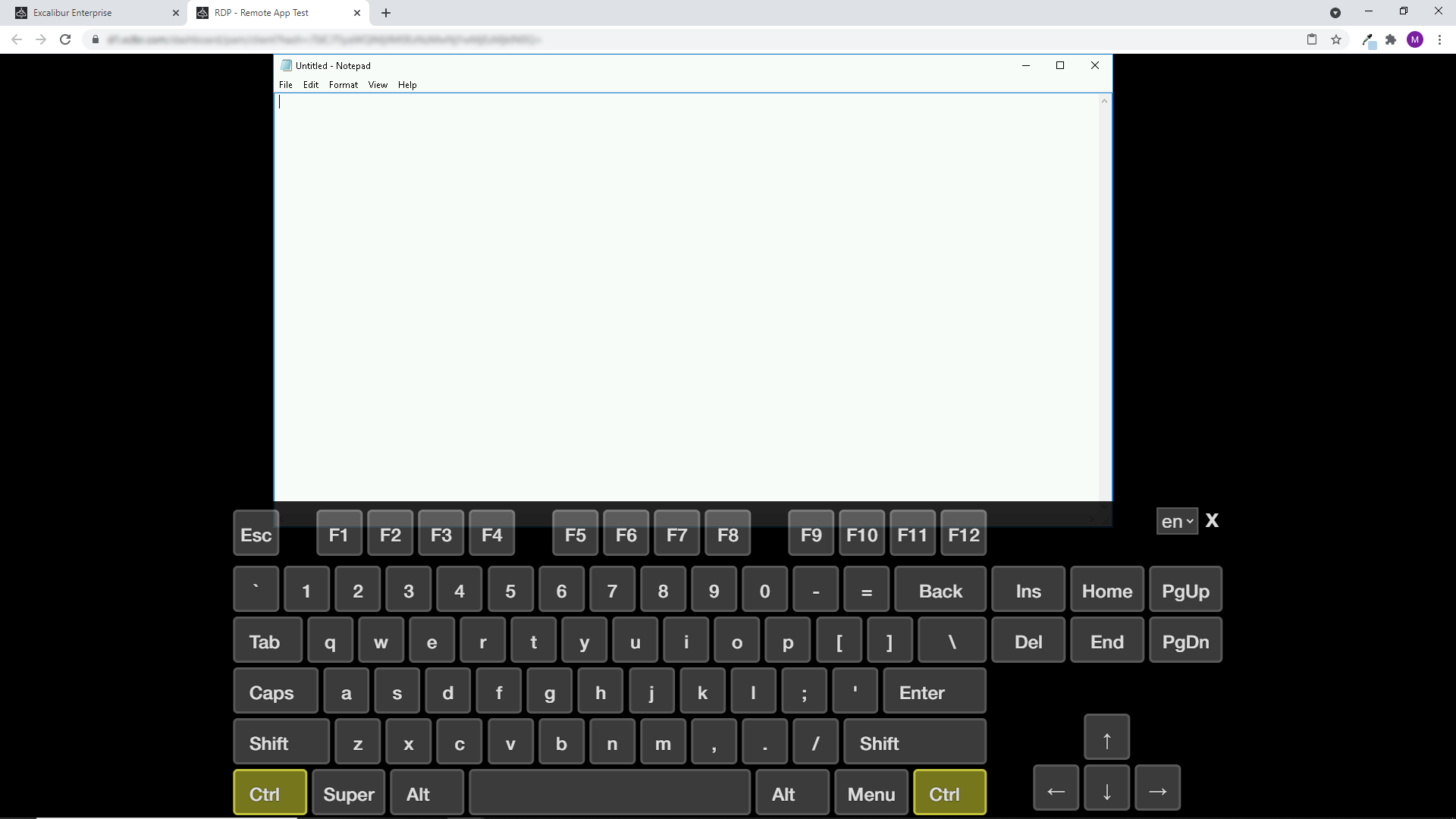
RDP example - Notepad RemoteApp¶
SSH example - Remote shell¶
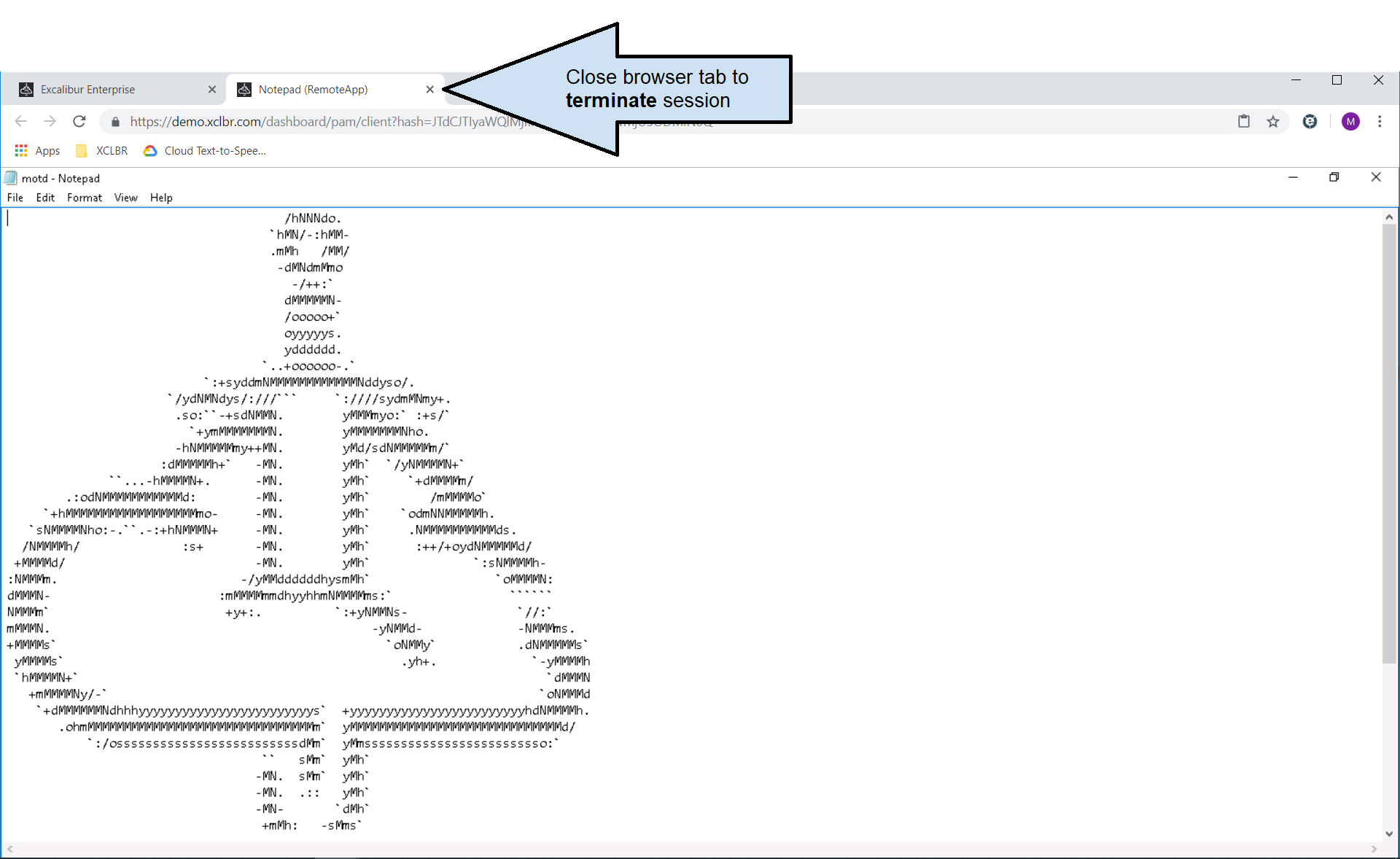
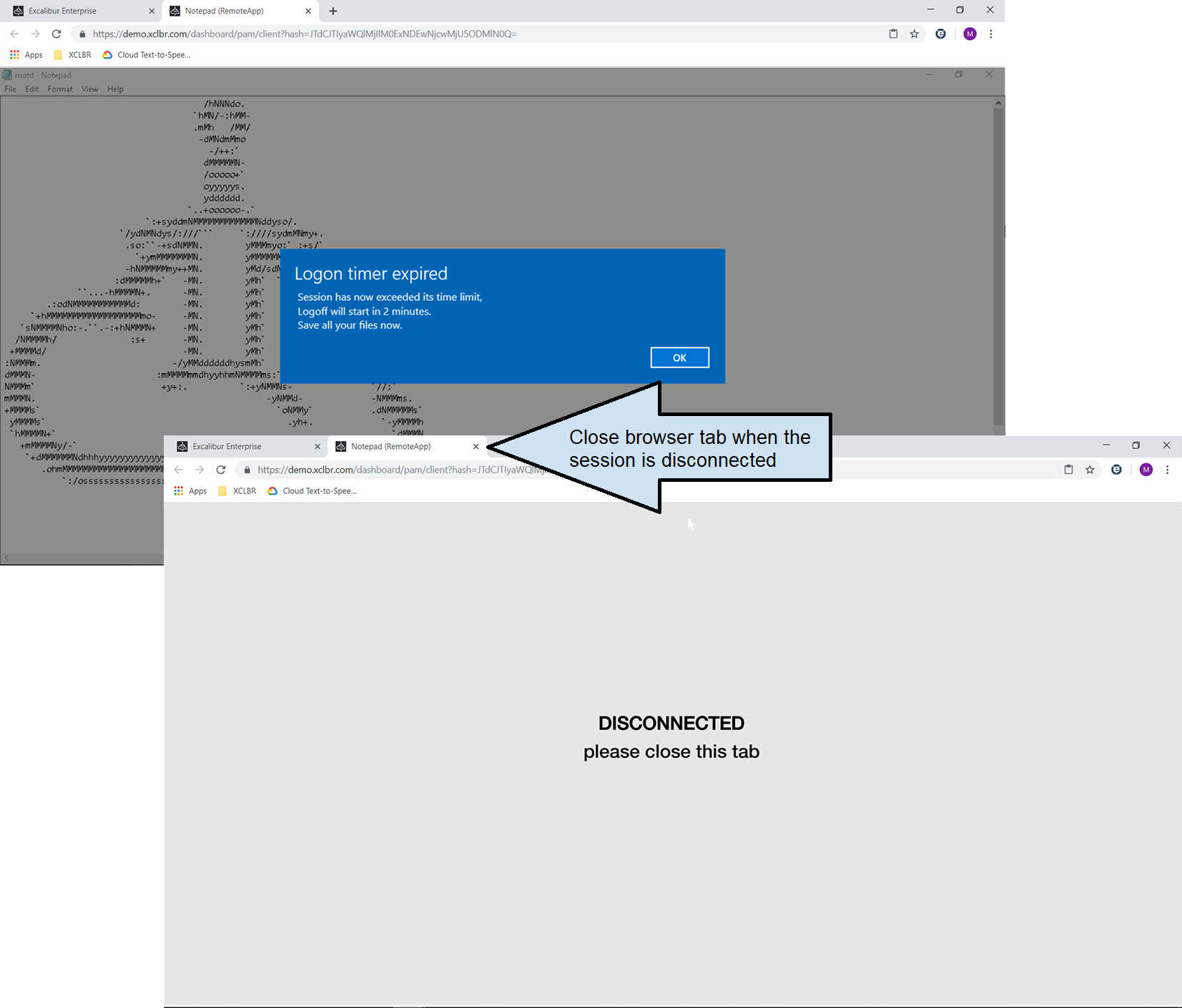
PAM session termination¶
Note
To conserve server resources, all RDP sessions have a one minute idle timeout
Windows integration¶
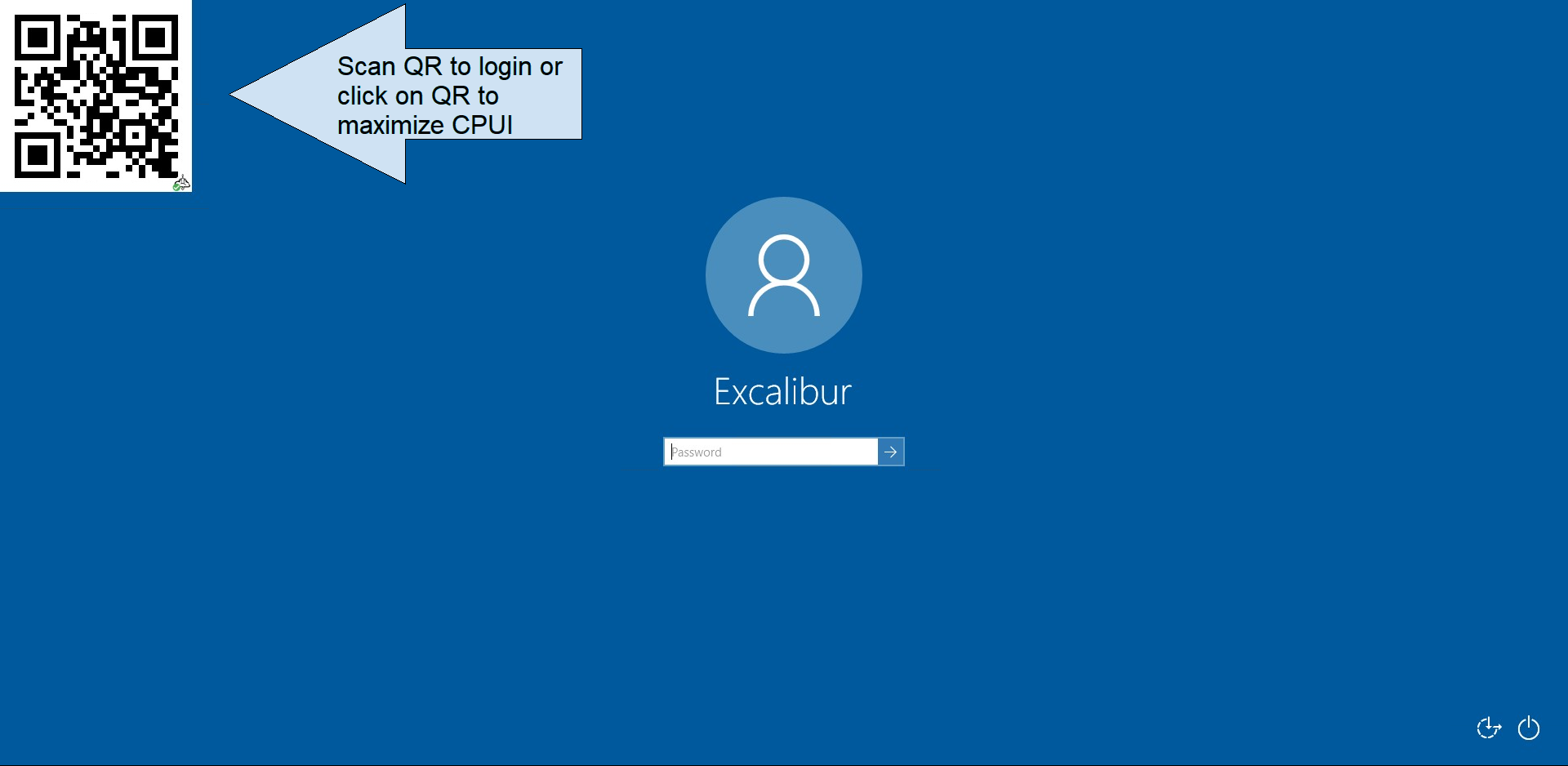
Excalibur Windows Operating System (OS) integration can be used for PAM resources too.. Excalibur PAM connects to the Server via RDP without any credentials (Network Level Authentication - NLA is disabled) - thus the Windows login screen will be shown. Notice the QR code in the top left corner of the login screen. If clicked-on Excalibur Credential Provider UI (CPUI) will be maximized. You can login to the machine by scanning the QR code exactly as when logging-in to the Excalibur Dashboard. This way zero-trust PAM can be created - a PAM that does not hold any user credentials at any time as authentication is performed directly in the OS where the user is logging-in.
PAM Management¶
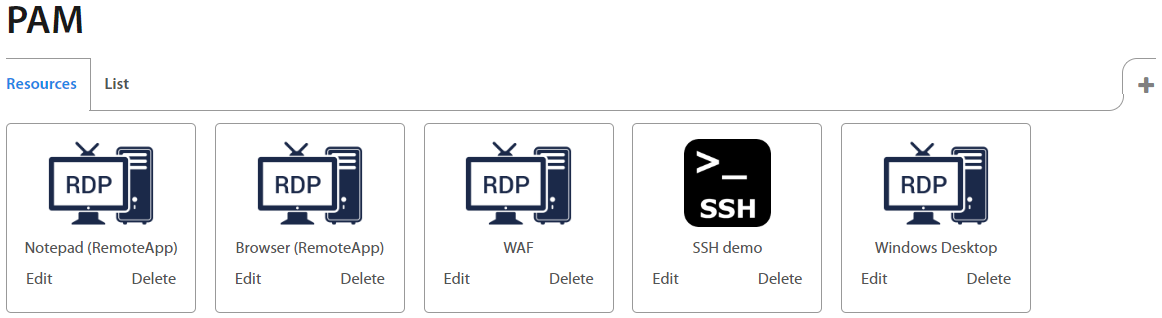
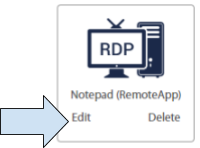
Users with administrator privileges have the option to create and manage PAM resources. By clicking on the “+” button at the top right corner, administrator can create a new PAM resource. By clicking on the Edit / Delete button under the name of Application, administrator can edit or delete applications.
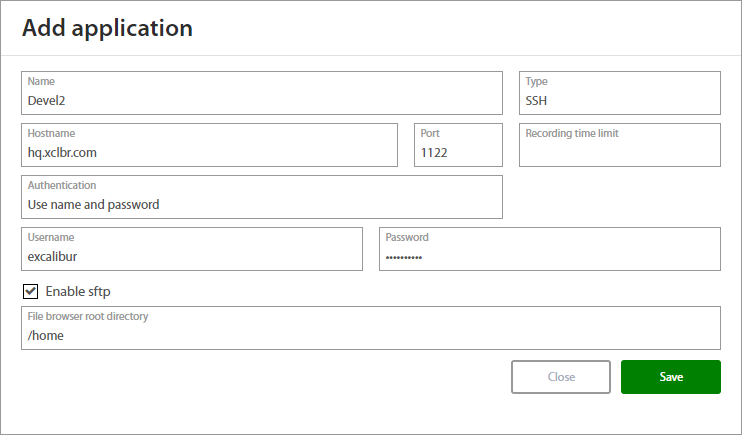
How to add the new PAM application¶
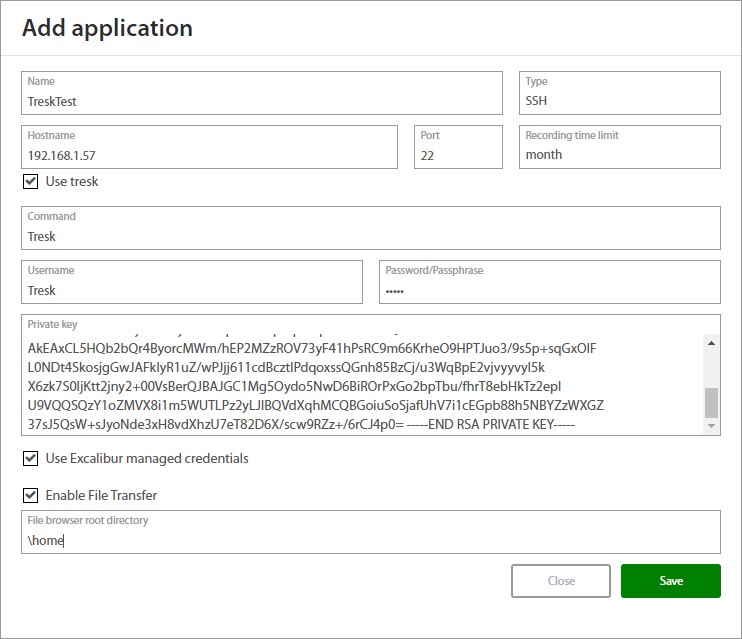
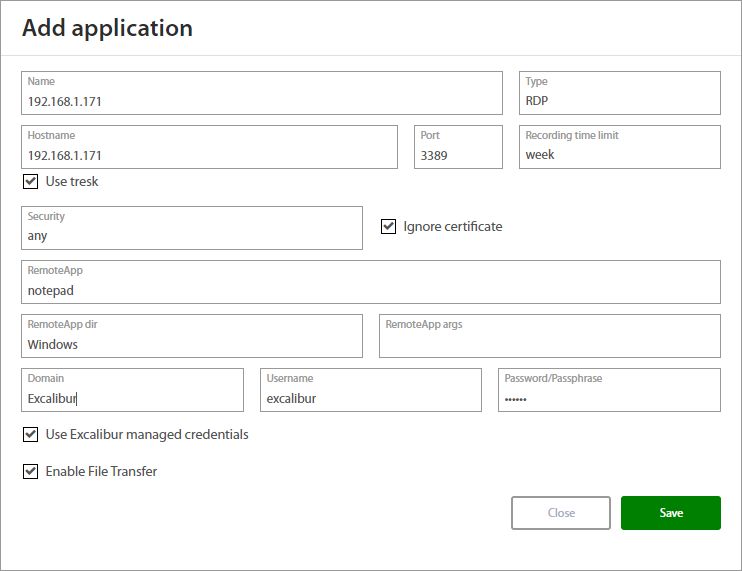
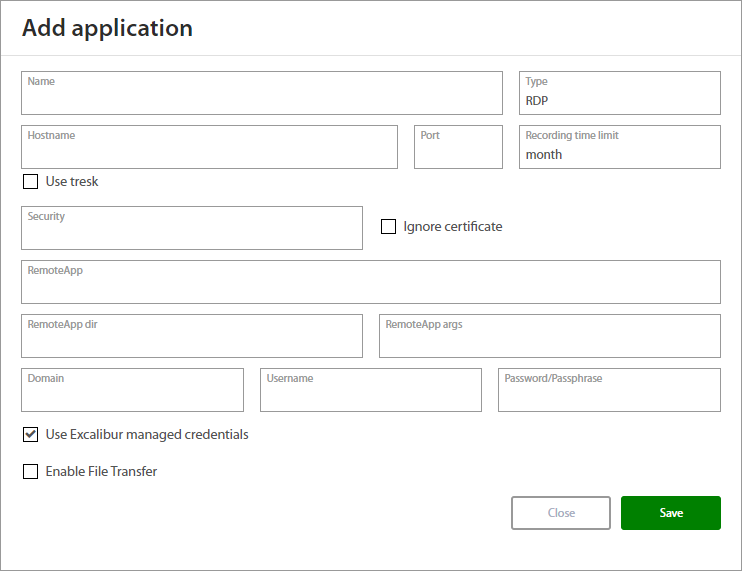
Click on the “+” button and the setting tab of the new application shows up. Fill in all fields and save the new connection. By selecting the Type, additional fields show up.
Basic setting tab.
SSH type¶
| Field | Description |
|---|---|
| Name | Name of application. |
| Type | SSH |
| Hostname | IP or hostname. |
| Port | Range 0 - 65535 |
| Recording time limit | Time limit how long will be recorded session stored on the server. |
| Use Tresk | If you wish to use a Tresk check this box. |
| Username | Fill username as Authentication factor. |
| Command | Type required command. |
| Password/Passphrase | Fill Password/Passphrase as Authentication factor. |
| Private key | Fill your private key. |
| Use Excalibur managed credentials | If this option is checked, the access to the PAM resource is verified by the user. |
| Enable file transfer | If you want transfer file, check this option. |
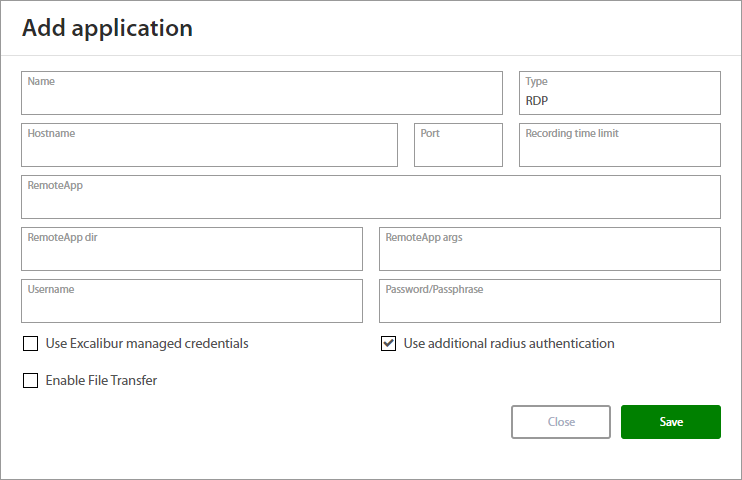
RDP type¶
| Field | Description |
|---|---|
| Name | Name of application. |
| Type | RDP |
| Hostname | IP or hostname. |
| Port | Range 0 - 65535 |
| Recording time limit | Time limit how long will be recorded session stored on the server. |
| Use Tresk | If you wish to use a Tresk check this box. |
| Security | Any, NLA, NLA-EXT, TLS, RDP |
| Ignore certificate | needs to be checked if the Terminal Server does not use a trusted CA certificate or the CA certificate it uses was not manually imported into the Excalibur PAM. |
| RemoteApp | Fill application which will be used (ex. paint.exe). |
| RemoteApp dir | Fill destination where application is located. |
| RemoteApp args | Set arguments for application. |
| Domain | Fill domain. |
| Username | Fill username as Authentication factor. |
| Password/Passphrase | Fill Password/Passphrase as Authentication factor. |
| Use Excalibur managed credentials | If this option is checked, the access to the PAM resource is verified by the user. |
| Enable file transfer | If you want transfer file, check this option. |
Notice the separated Domain and Username fields - do not enter the domain name in the username field - always use the separate input elements
RDP PAM configuration description can be found in Excalibur PAM - RDP connection setup manual
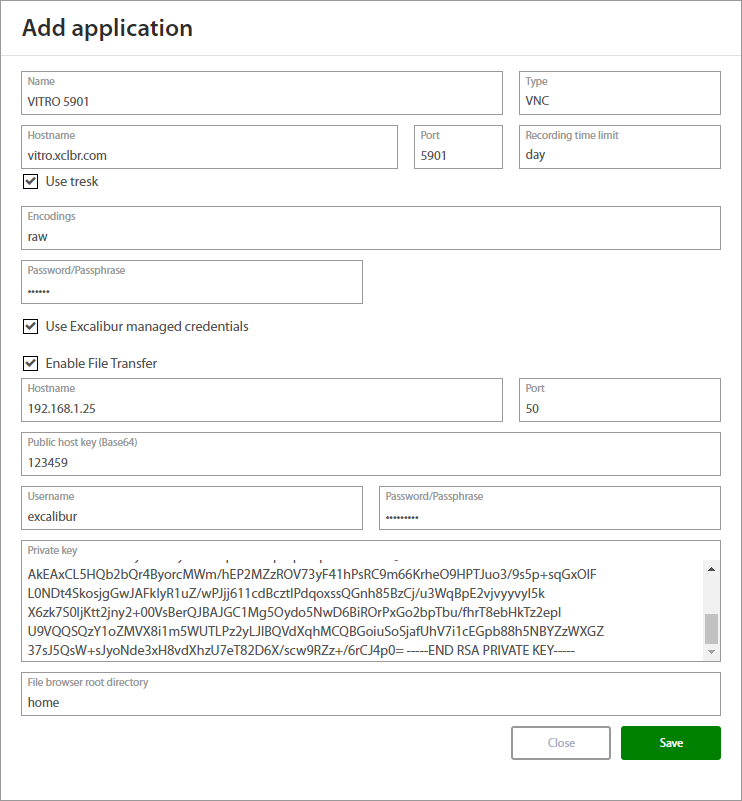
VNC type¶
| Field | Description |
|---|---|
| Name | Name of application. |
| Type | VNC |
| Hostname | IP or hostname. |
| Port | Range 0 - 65535 |
| Recording time limit | Time limit how long will be recorded session stored on the server. |
| Use Tresk | If you wish to use a Tresk check this box. |
| Encodings | Format which will be used. |
| Password/Passphrase | Fill Password/Passphrase as Authentication factor. |
| Use Excalibur managed credentials | If this option is checked, the access to the PAM resource is verified by the user. |
| Enable file transfer | If you want to transfer file, check this option and fill the fields below. |
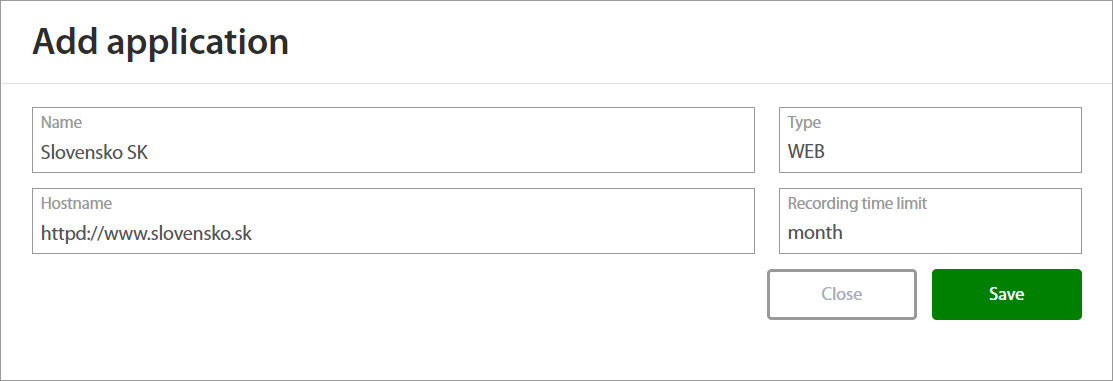
WEB type¶
Web type uses a HTTP Proxy protocol and provides an accesss to resources with recording of user's activity.
| Field | Description |
|---|---|
| Name | Name of application. |
| Type | WEB |
| Hostname | IP or hostname. Type with protocol e.g. https:// |
| Recording time limit | Time limit how long will be recorded session stored on the server. |
Tresk¶
TRESK allows access to any Target inside the Intranet with almost zero infrastructure or policy (re)configuration. TRESK is responsible for establishing and managing connections between Target and TRESK-Server, either via TRESK-Client or TRESK-V3-VM. For more information about TRESK see Tresk Manual
If you want to use tresk, just check the “Use tresk”
Managed credentials¶
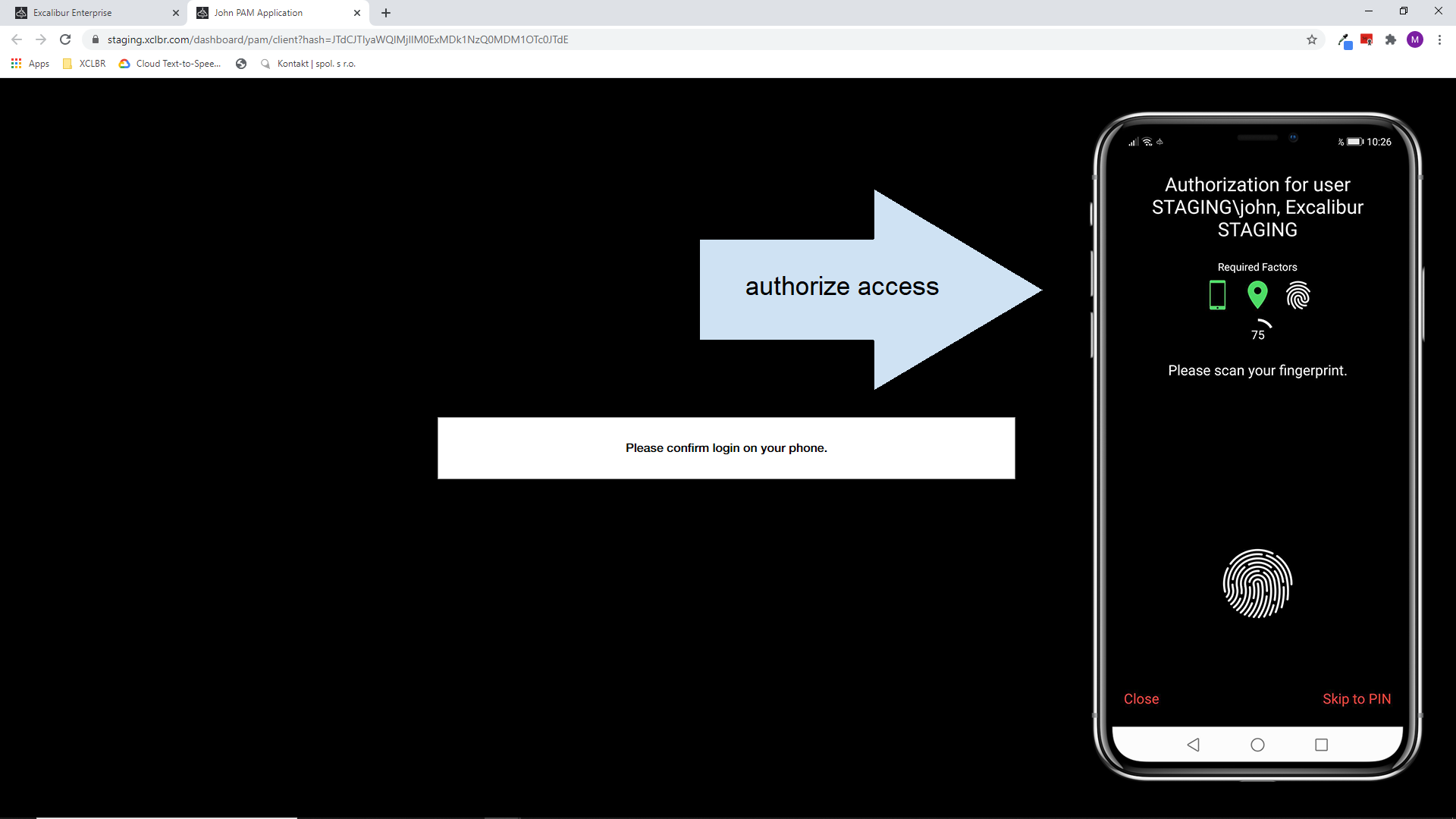
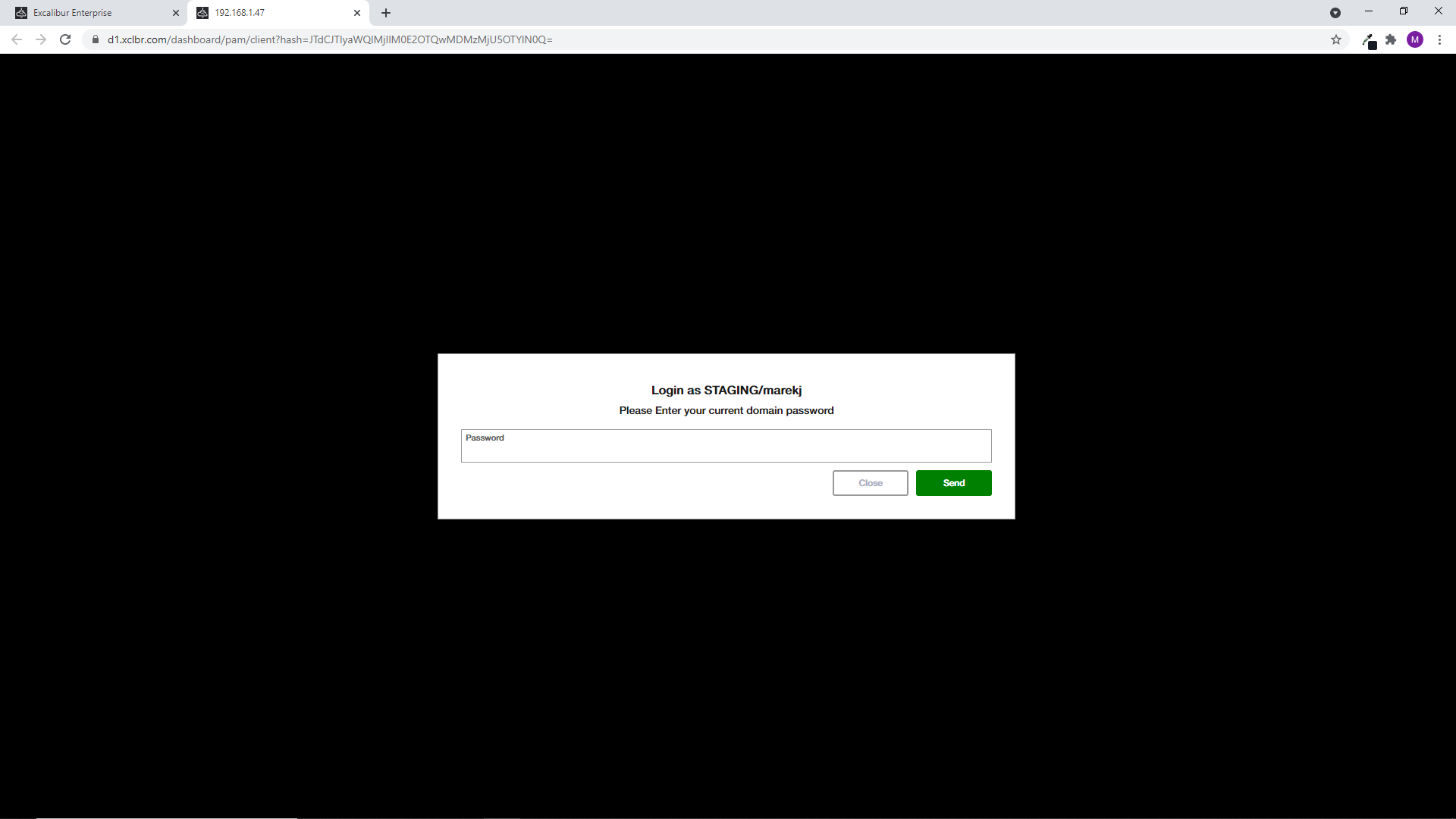
Excalibur allows you to set static credentials for access to the PAM resource or use managed credentials for access to the PAM resource. Managed credentials means that user’s credentials are automatically managed for the PAM resource. Each user’s access must be manually verified. User confirms the PUSH notification on the token, and provides factors for access to the PAM resource.
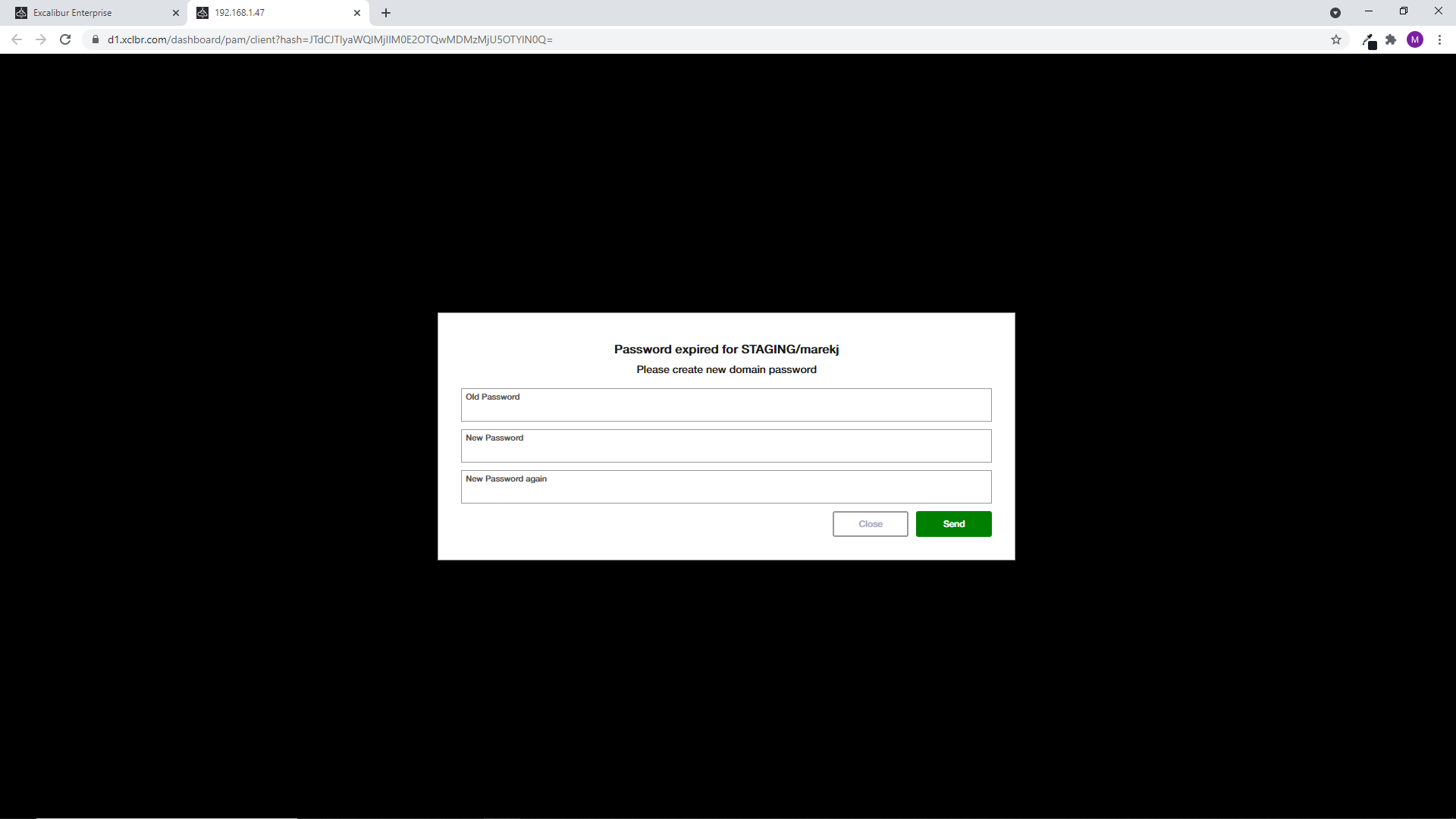
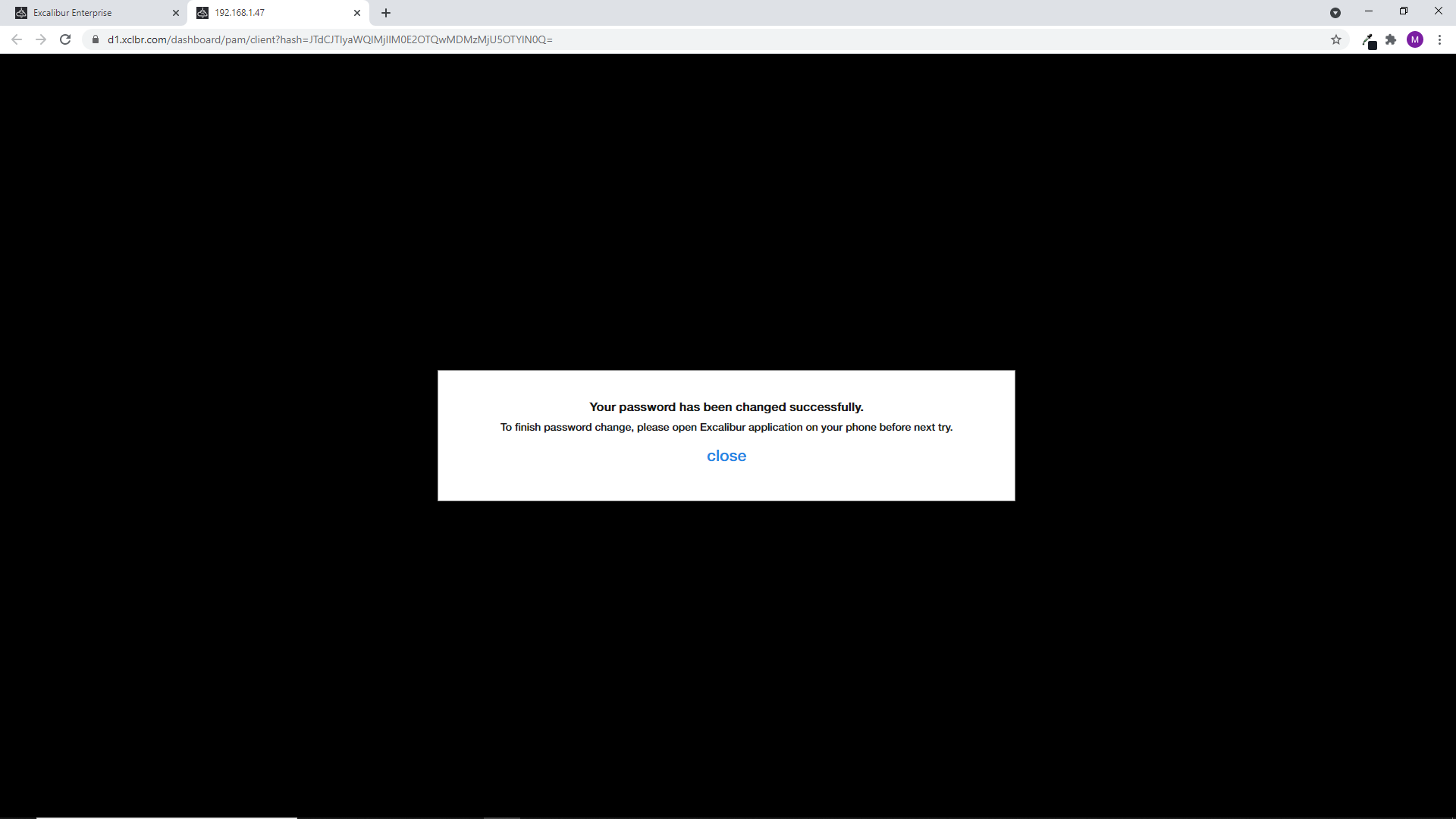
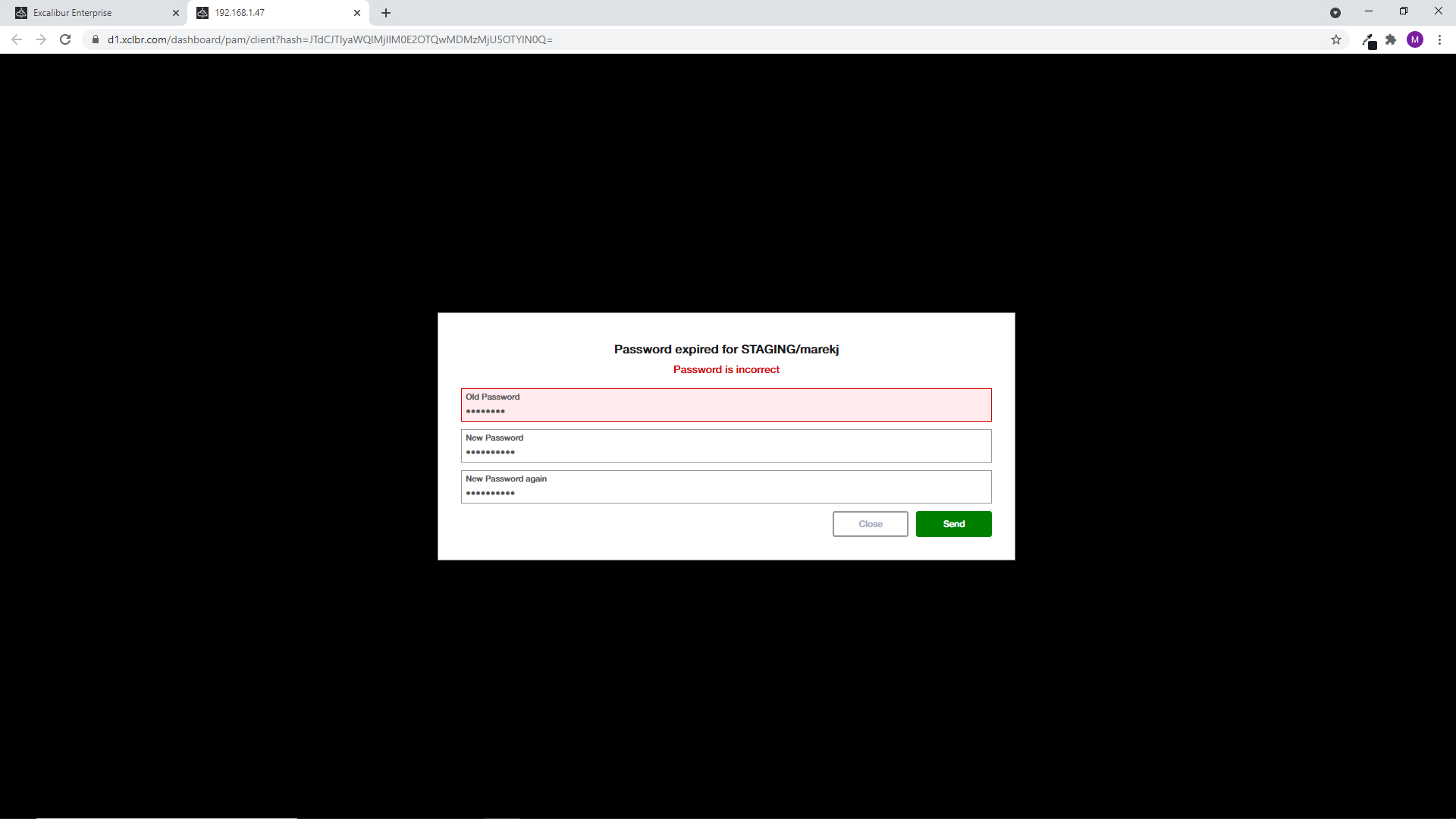
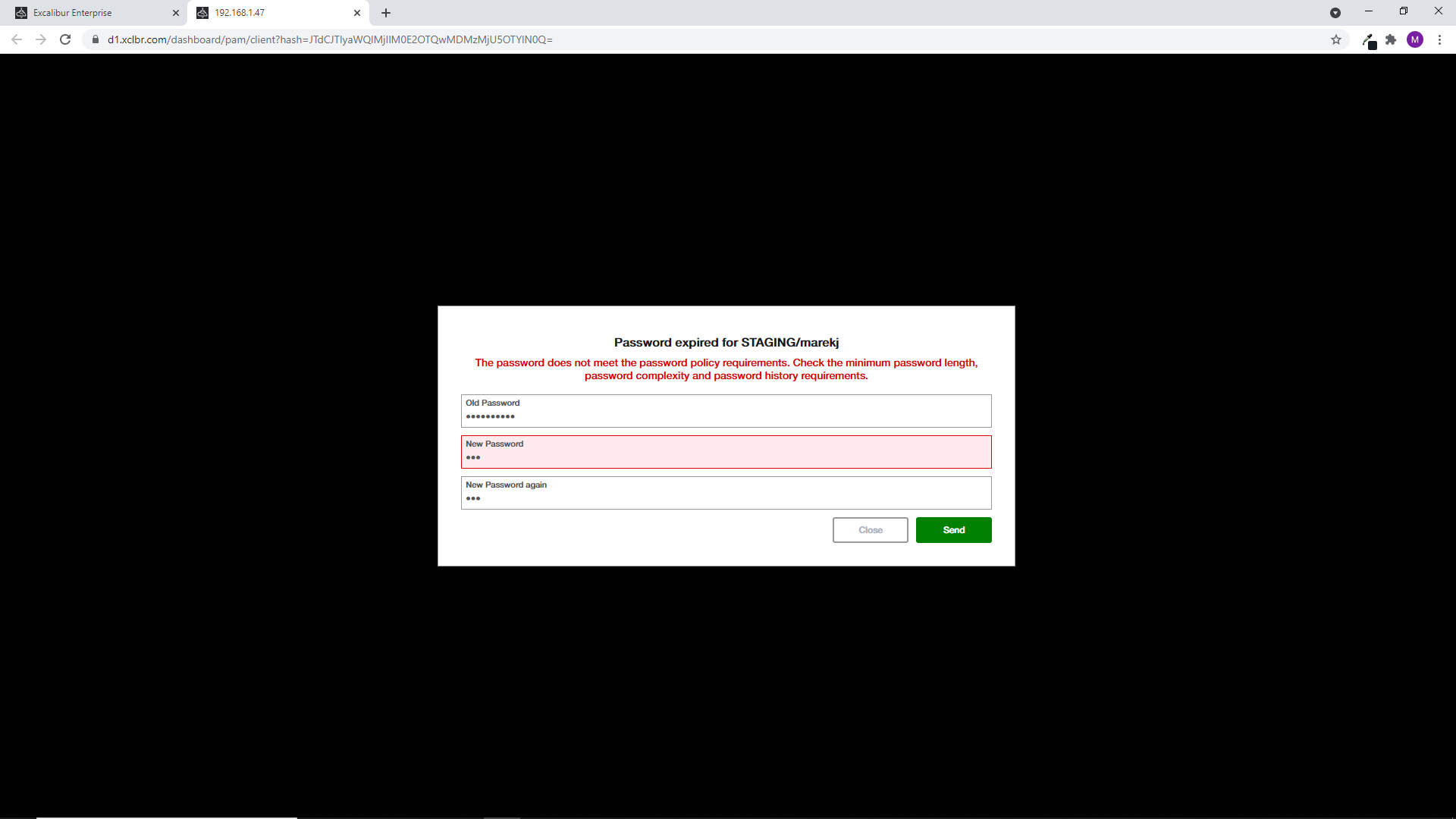
Expired / Static password¶
When the password is expired or reseted, Excalibur asks you to provide a new password. After successful change, close the PAM session tab and open the new.
Excalibur informs you if the password is incorrect or does not meet the password policy requirements.
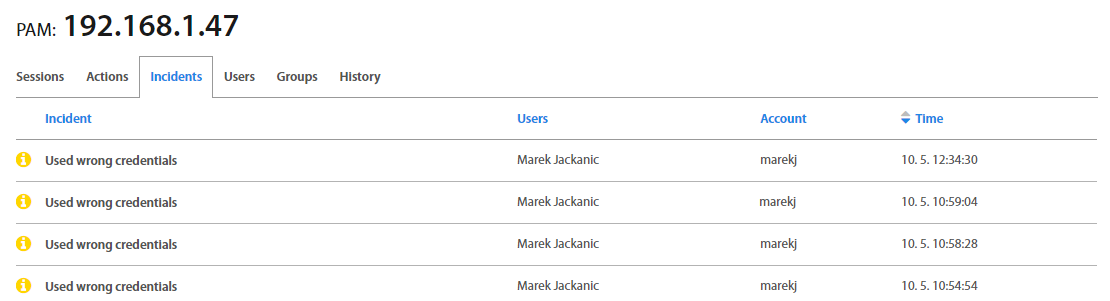
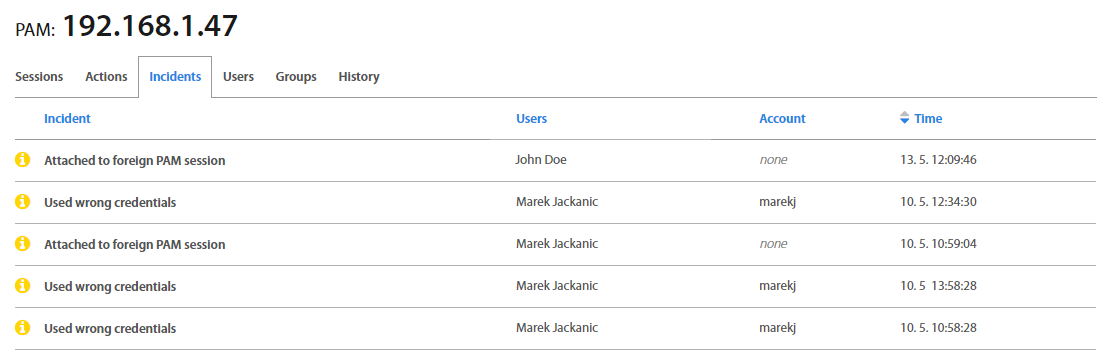
Authorization to the PAM resource as well as access with incorrect credentials are recorded into tabs.
RSA SecurID¶
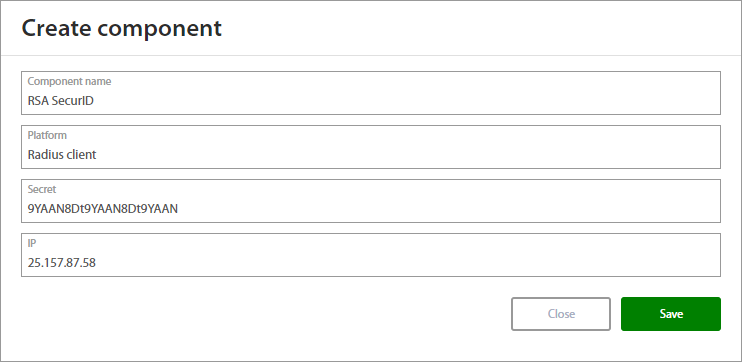
Excalibur PAM allows use an additional authentication such as SecurID. This solution is based on RADIUS protocol. To use the SecurID is necessary to create component for SecurID and following to set additional authentication.
Click on the Components on the left menu and create a new Radius client component and define fields:
| Field | Description |
|---|---|
| Component name | Name of component. |
| Platform | Select Radius client. |
| Secret | Type Secret. |
| IP | Address of the RADIUS server where the OTP code from the RSA SecureID token is verified. |
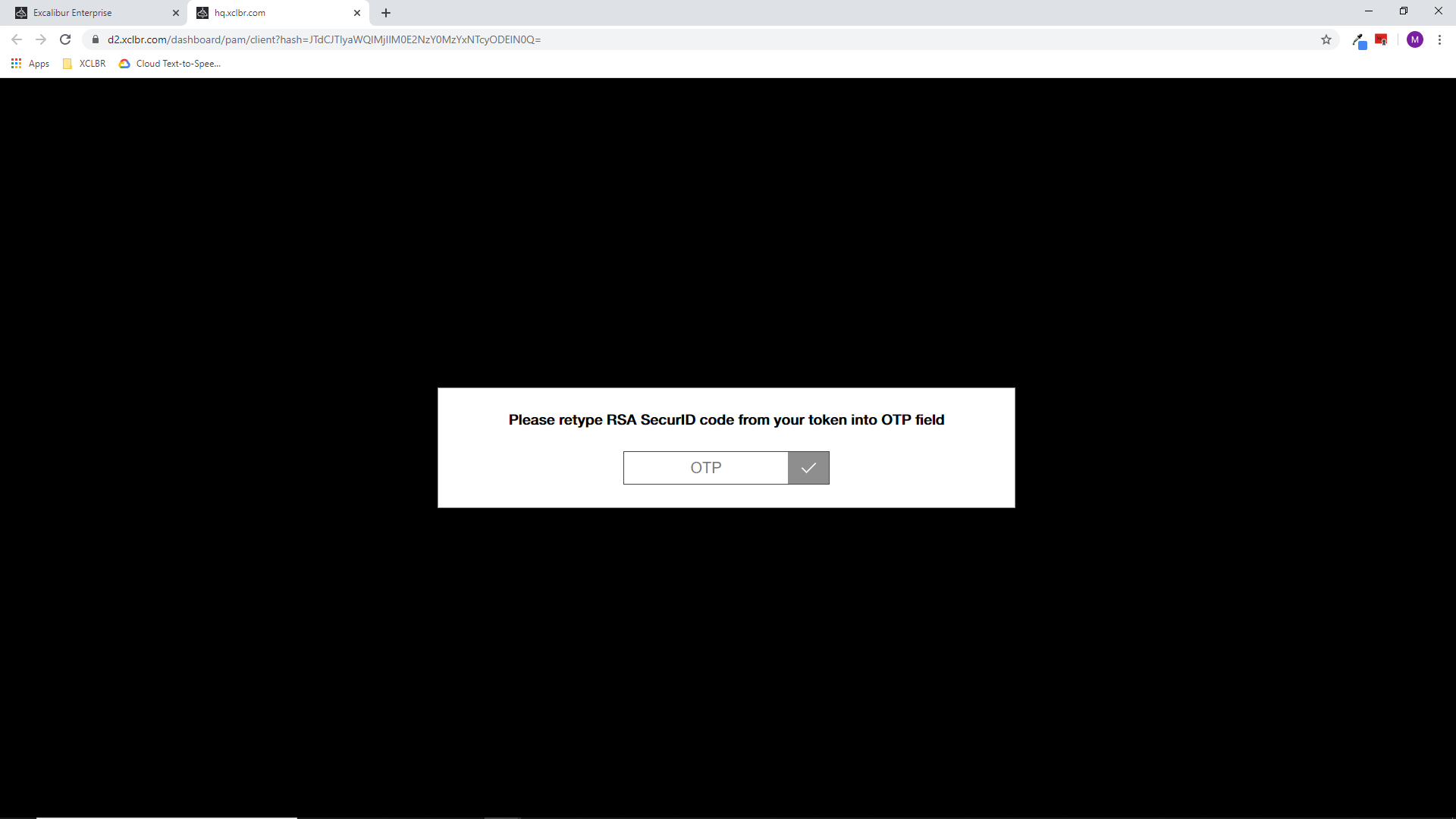
When the component is created, check “Use additional radius authentication” for the specific PAM resource and save the changes. From this moment, each access to the PAM resource requires an OTP code from the RSA SecureID token.
How to edit PAM application¶
If the application's settings is necessary to change, click on the Edit button, edit settings and save changes.
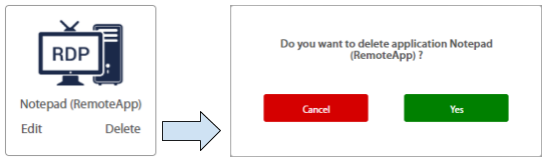
How to delete PAM application¶
How to assign PAM application to user¶
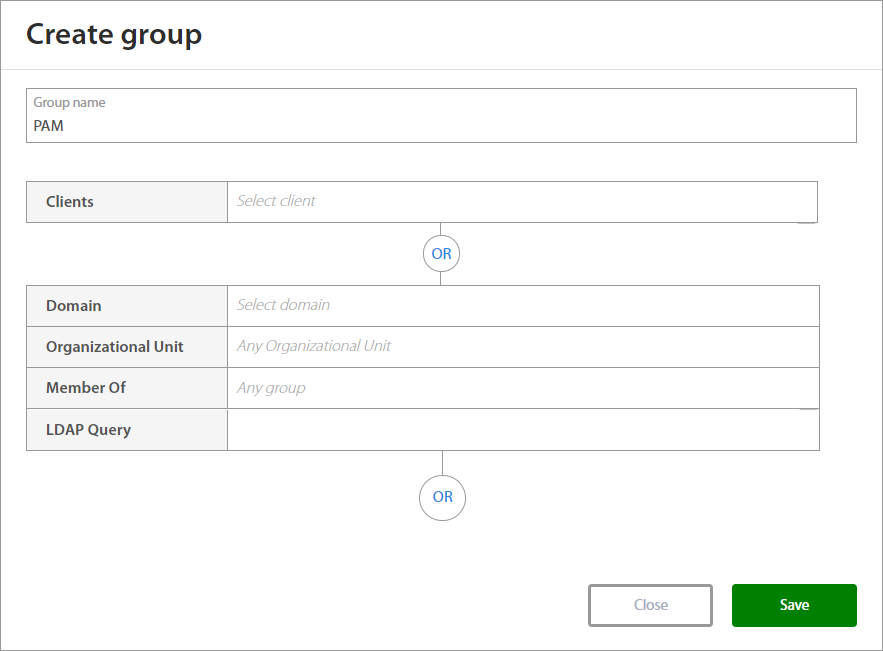
Excalibur is configured via Groups allowing for matching a user group (defined for example by an LDAP filter) to a particular security policy and a particular group of published PAM resources. First step is to assign the new PAM connection to a computer group. Click on Computers groups on the left menu and select or create the Computer group. Fill the name of the application to the Clients field and save it.
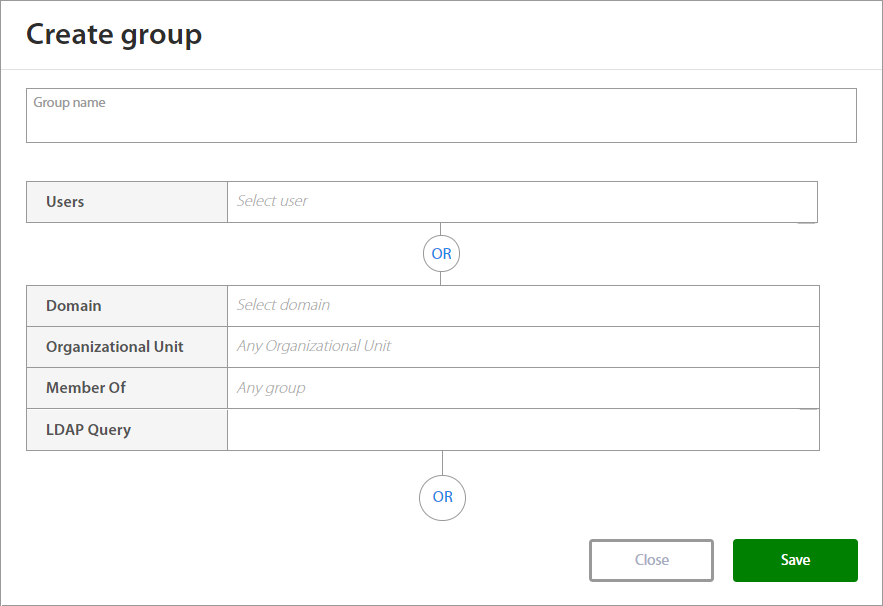
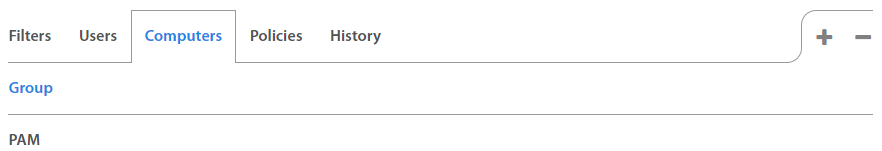
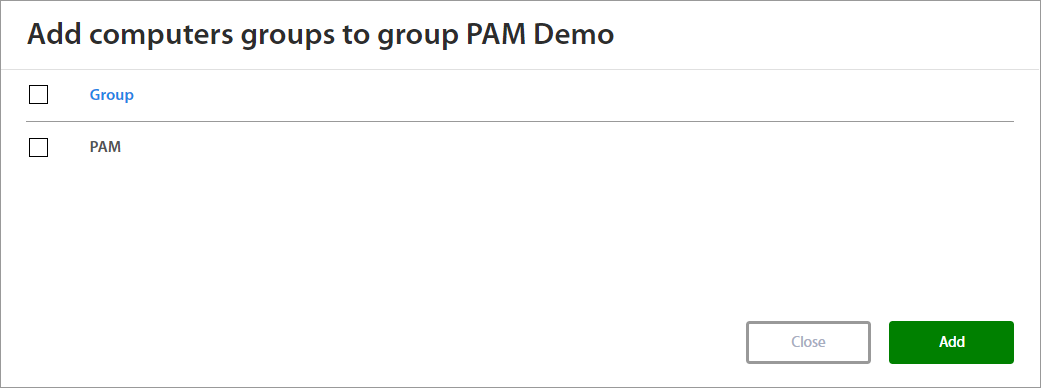
The next step is to assign the Computer group to the User Group. Click on Users groups on the left menu and create or select the User group. By clicking on the selected user group, the group details show up. Select Computers tab and click on the “+” button to add Computer group to User group. Select the group or groups and confirm by the Add button. When necessary to unassign the computer group, click on the “-” button and select groups which you want to unassign and confirm change.
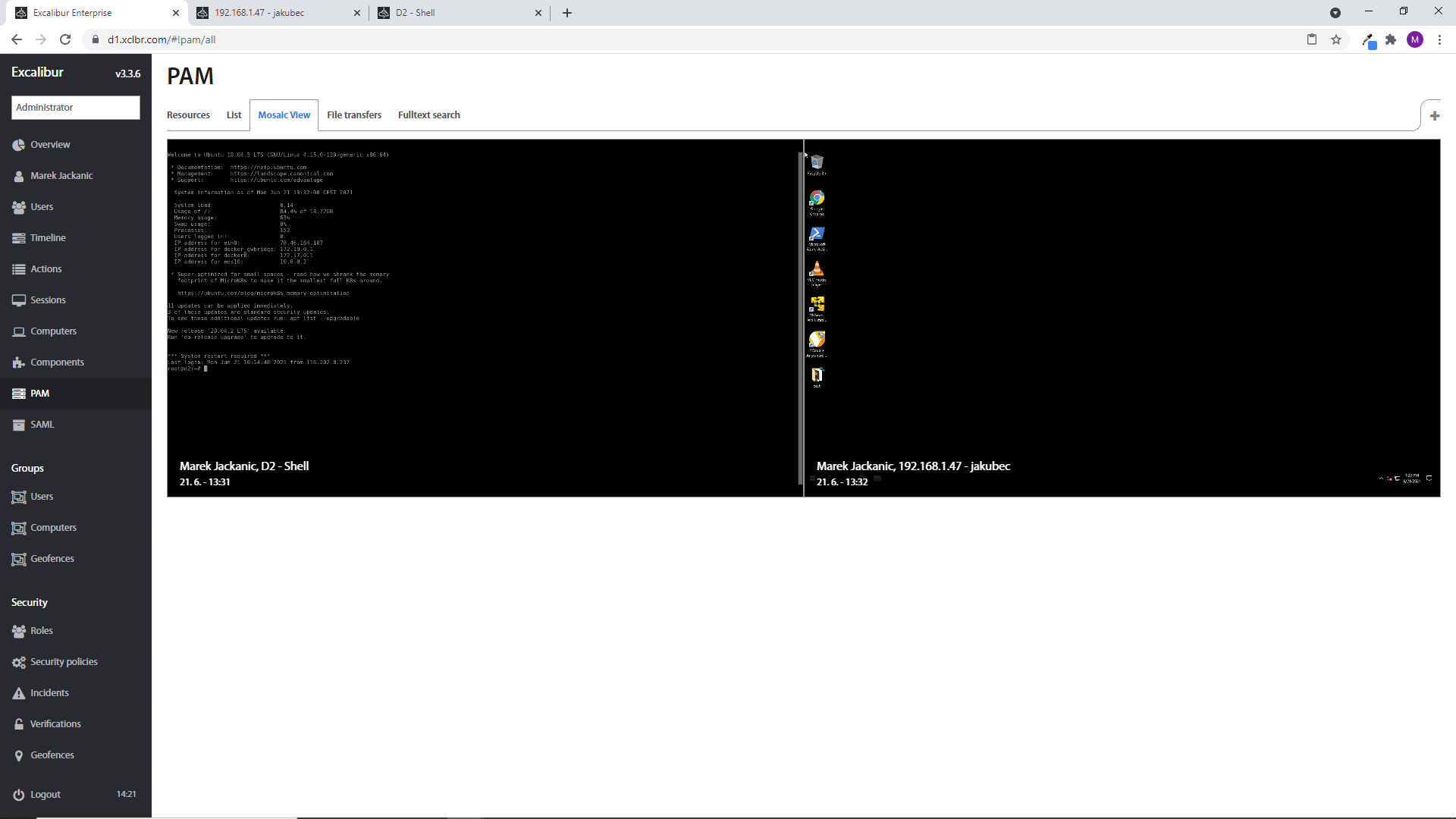
How to see what another user is doing 1¶
Excalibur PAM provides an option to see activity of another user during the user's PAM session. Click on the List tab on the PAM section, click on the required PAM resource and PAM details show up. Hover over the required active PAM session and buttons show up. Click on button and you will attached on selected PAM session in new tab. In this case, you can not interact with the PAM resource. You can only see what another user is doing.
Note
HTTP proxy session can not be previeved
How to see what another user is doing 2¶
The active PAM sessions can be previewed in Mosaic tab. In case that the PAM session is closed / opened then preview screen is automatically removed / added. Preview screen contains: Name of user who works in PAM resource, Name of the PAM resource, date and time. As in a previous chapter, the event of attaching to the PAM session is recorded in the Incident tab of the specific PAM resource. Manager can attach to subordinates session. Administrator and Auditor can attach to all sessions.
Note
HTTP proxy session can not be previeved.
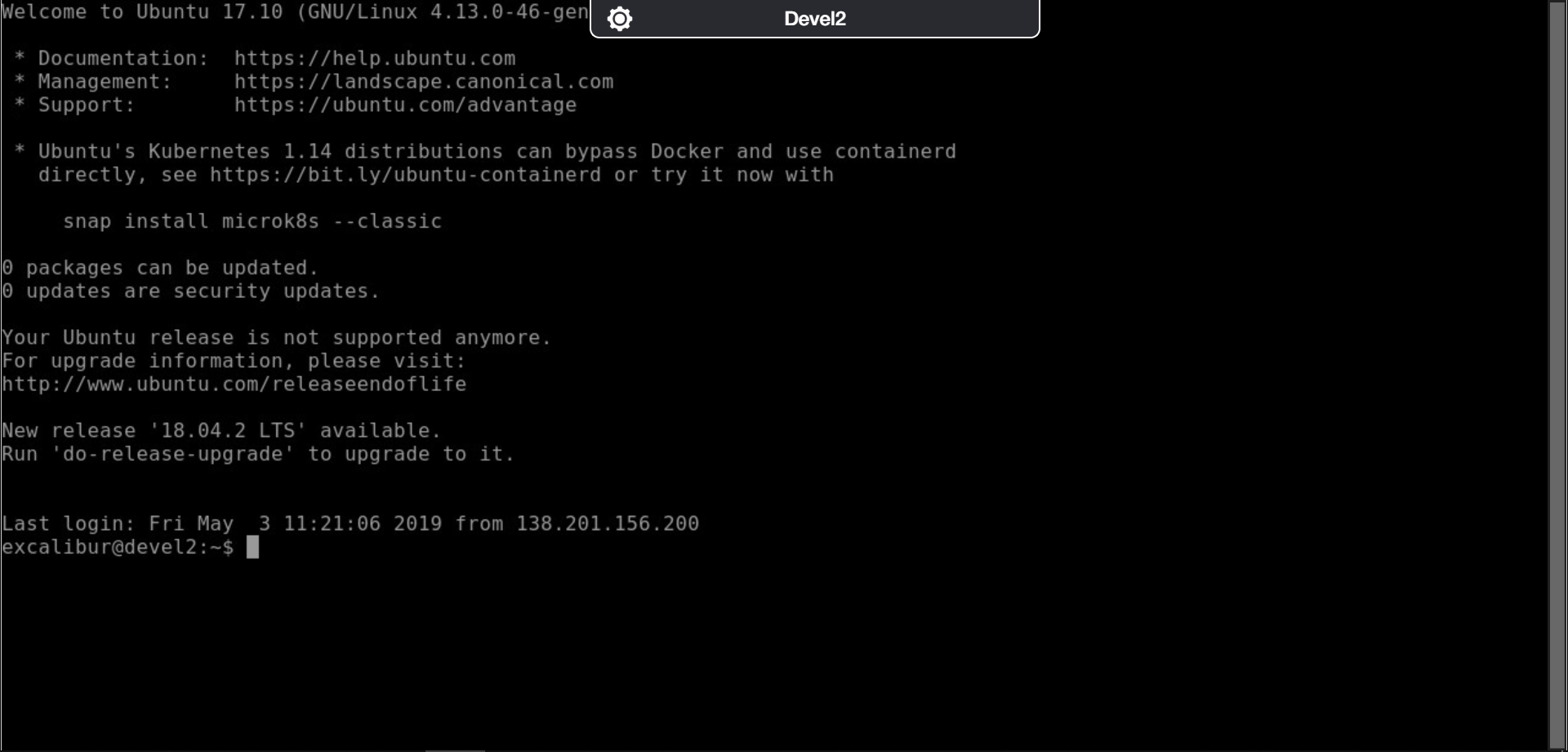
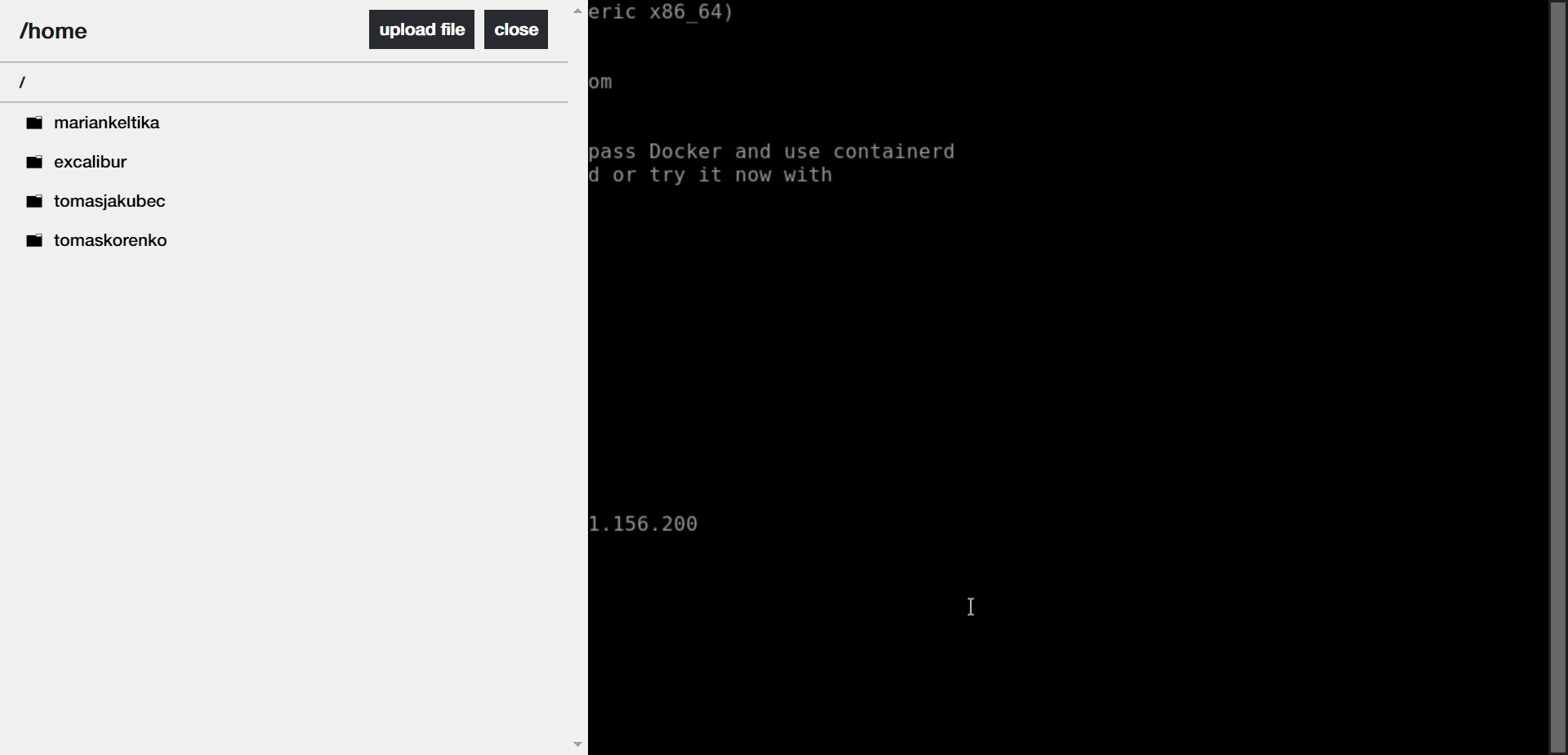
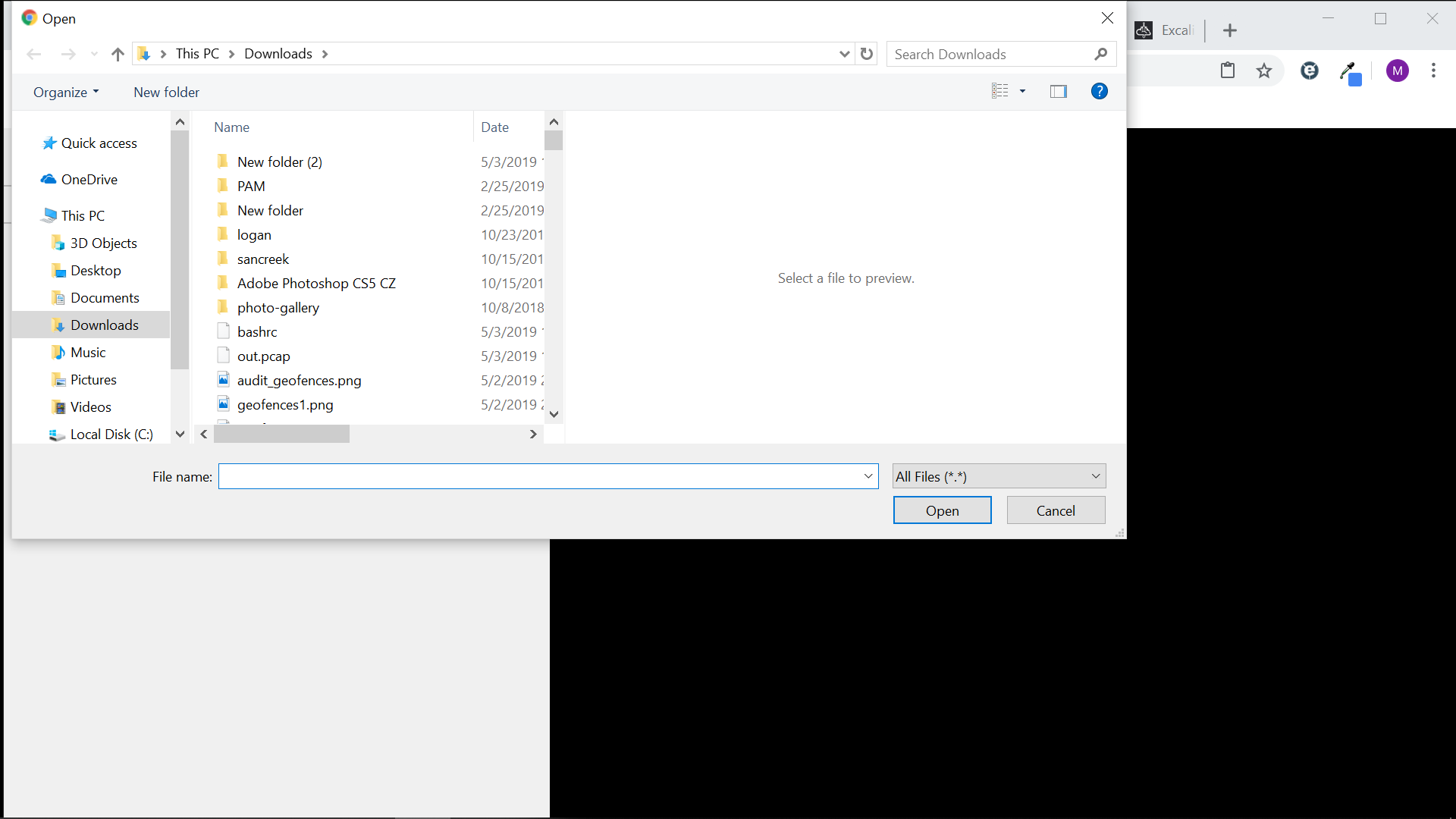
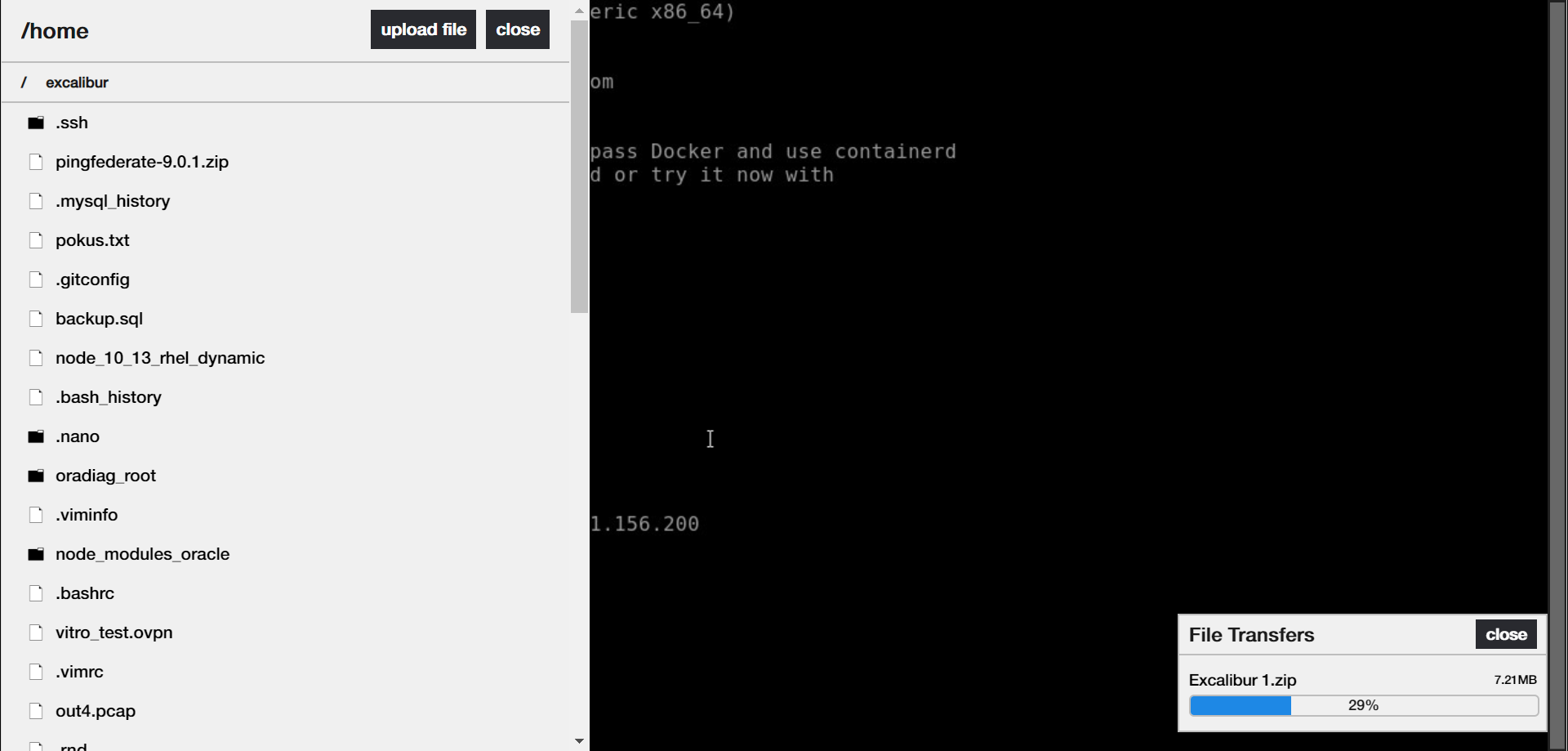
How to transfer file (SSH example)¶
PAM resources provide an option to transfer files. If file transfer is needed, Enable sftp has to be ticked and File browser root directory has to be setup.
Launch the desired SSH application, and the connection is opened in a new tab. At the top of the application session’s tab is the setting bar. Click on the button and panel on the left side shows up.
Click on device and select destination where you want to upload/download the file. If you want to download a file, double click on the selected file, and the file is downloaded immediately. To upload a file, select the destination where you want to upload the file and click on the Upload button. Select the desired file and upload it. Files which are uploaded, they are impossible to delete without elevated privileges.
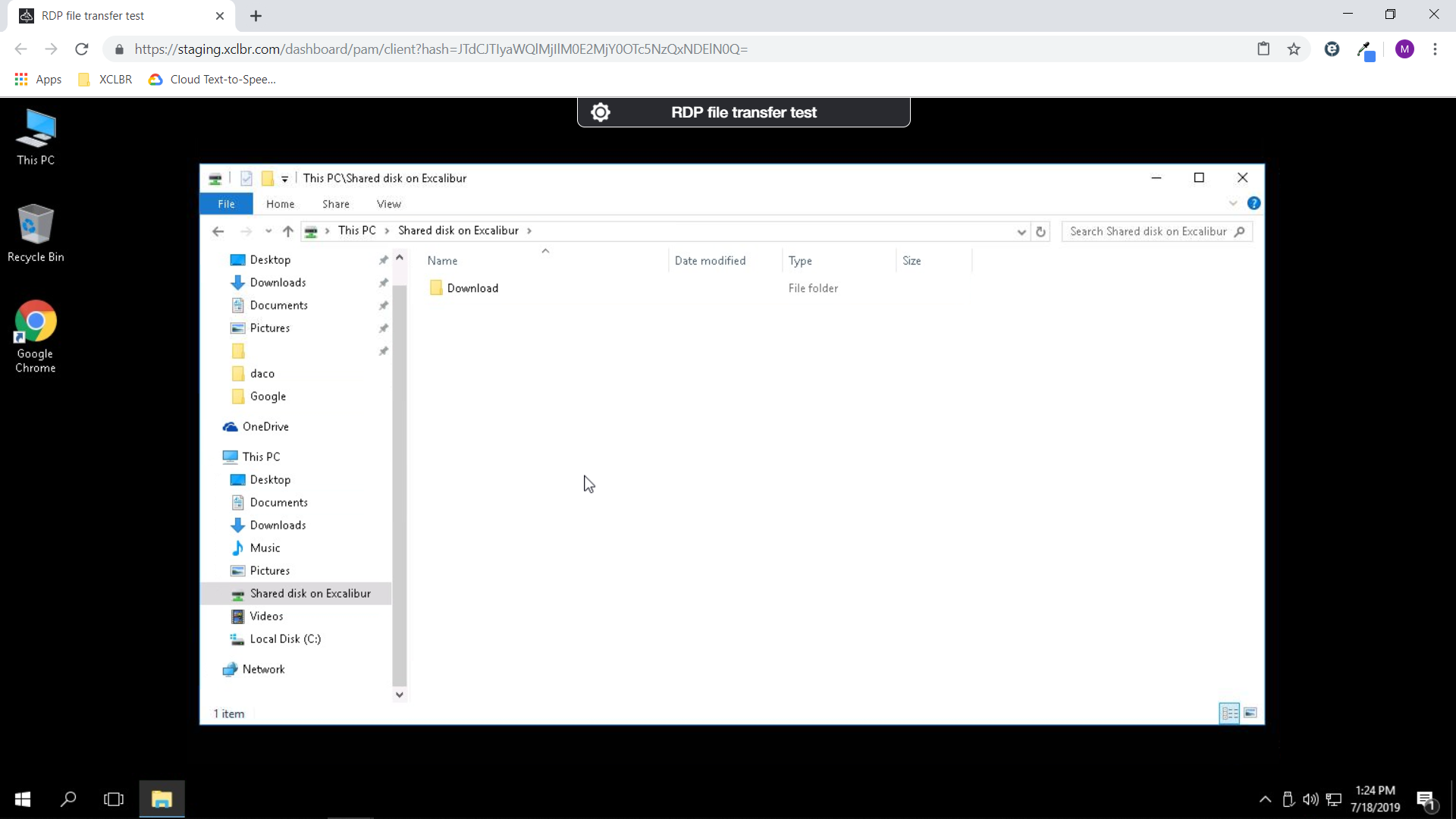
How to download file (RDP example)¶
Principle of the file transfer on an RDP connection is the same as SSH. If it is needed to download a file from another destination as is set on PAM Setting, copy required file to “Shared drive on Excalibur” at the first /you can found it in This PC window/, and then copy file to Download folder. The file is downloaded to your computer immediately.
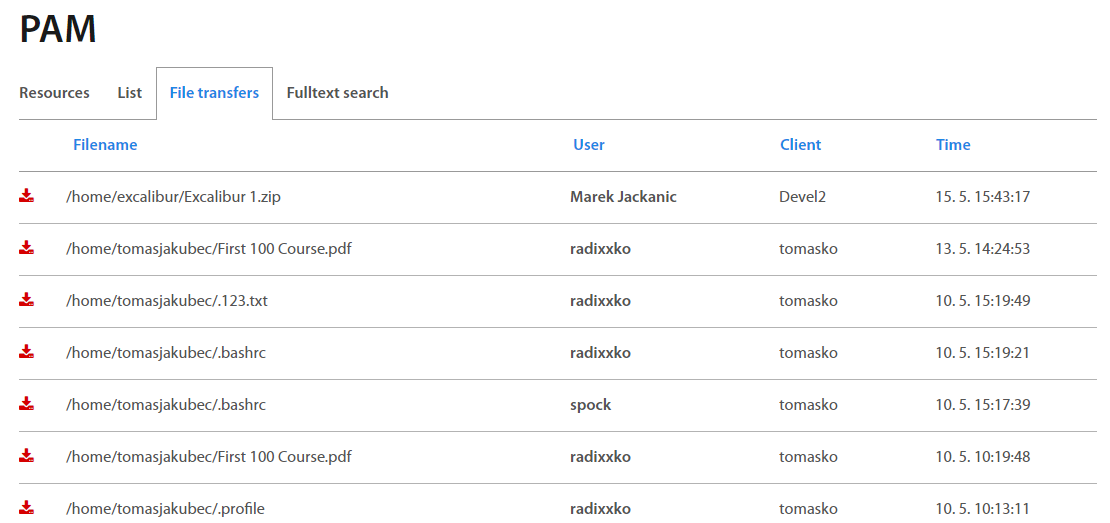
How to review and download transferred file¶
Excalibur PAM displays all files which are transferred by users in PAM sessions. Each role has presetted rules to show transferred files. For Administrators, Service desks and Auditors are shown all files, managers have access to their own and subordinate’s files. Users have access to their own files only. The transferred files are stored in the internal Excalibur space, regardless of the recorded sessions. Files are still available after deleting a sessions.
Switch to File transfers tab on PAM section and there is a list of transferred files with further information about file and its destination; user who upload/download file; client; date and time of transfer. By clicking on the specific file or / button, the file is downloaded immediately. By clicking on the user name or client, further information is shown.
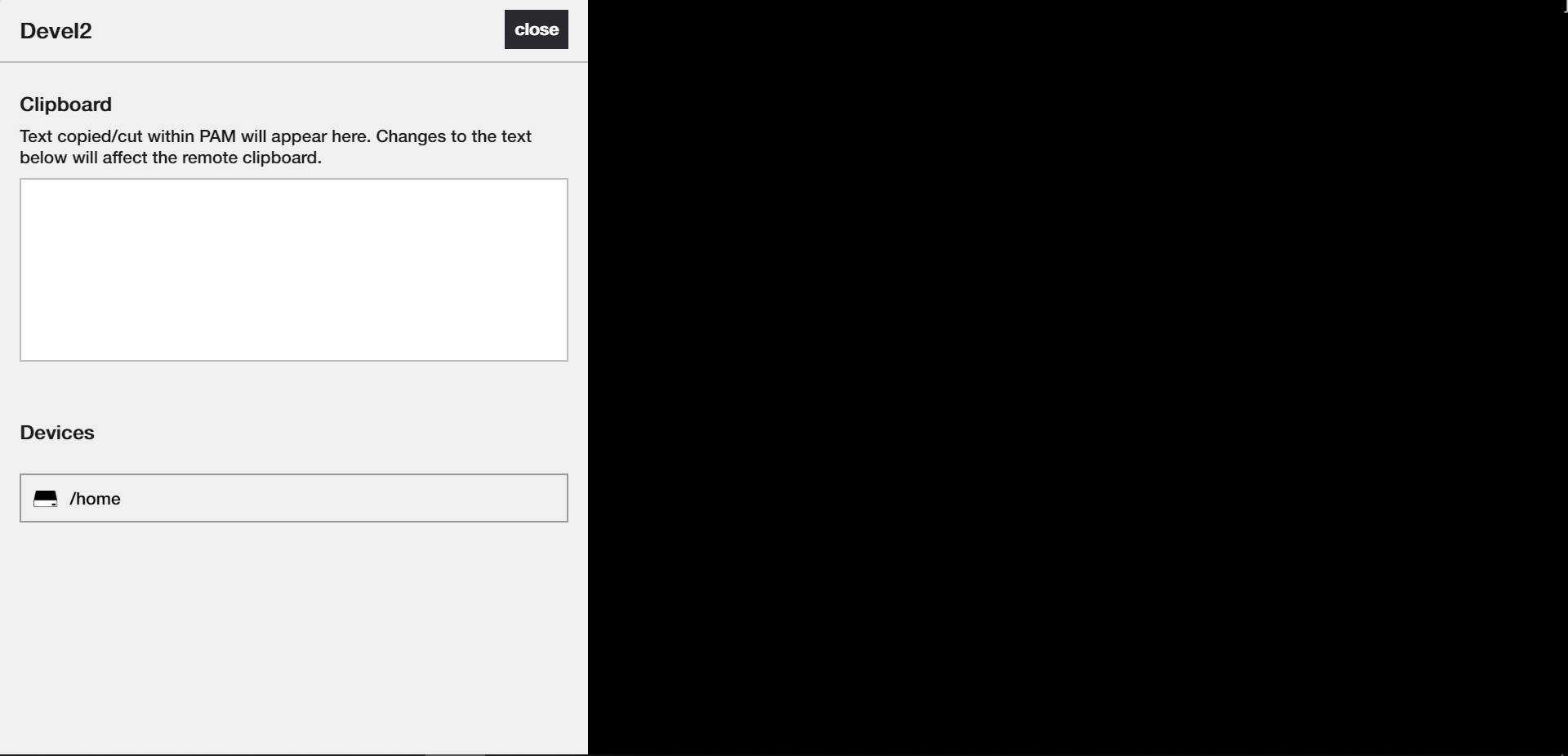
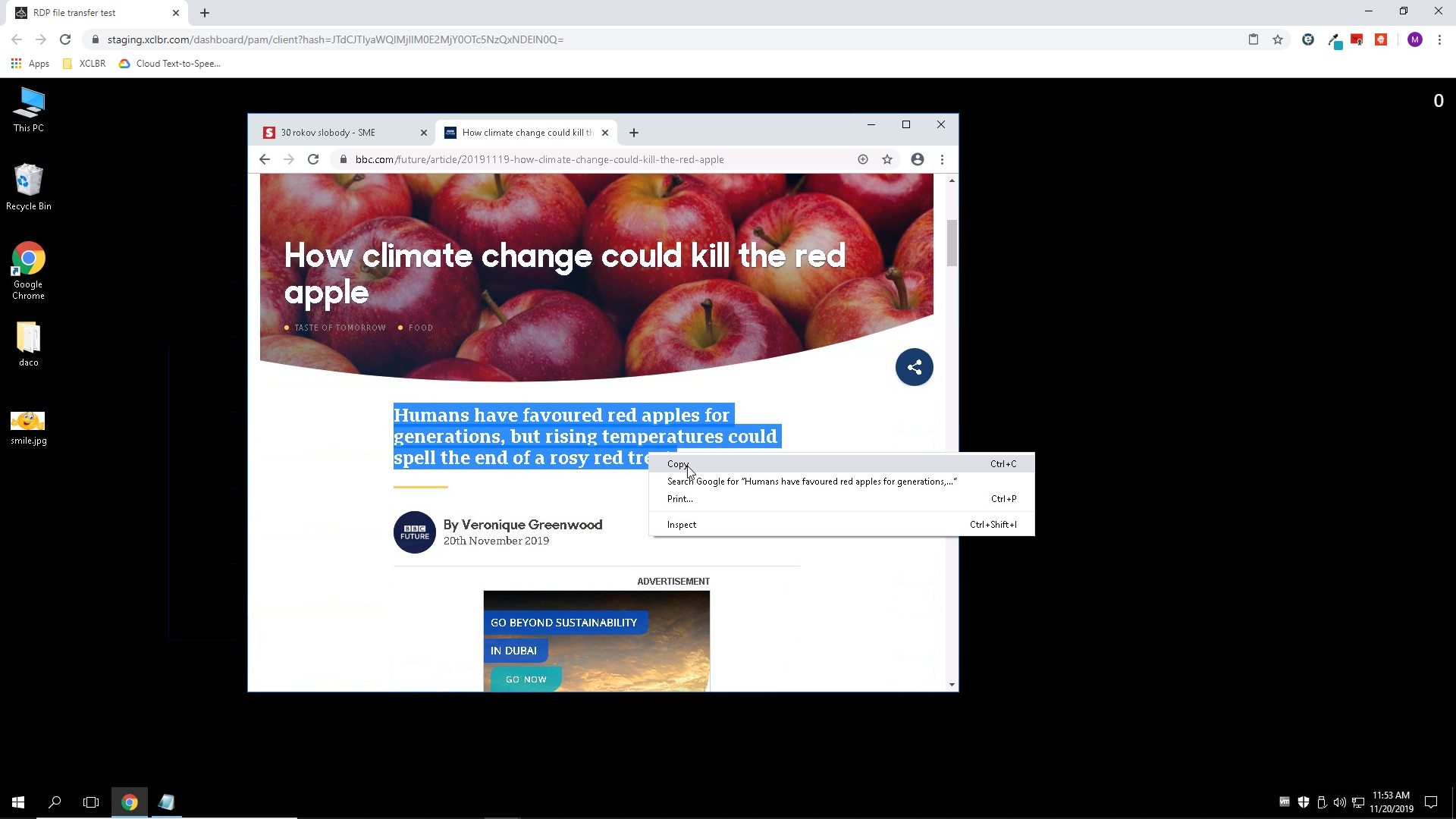
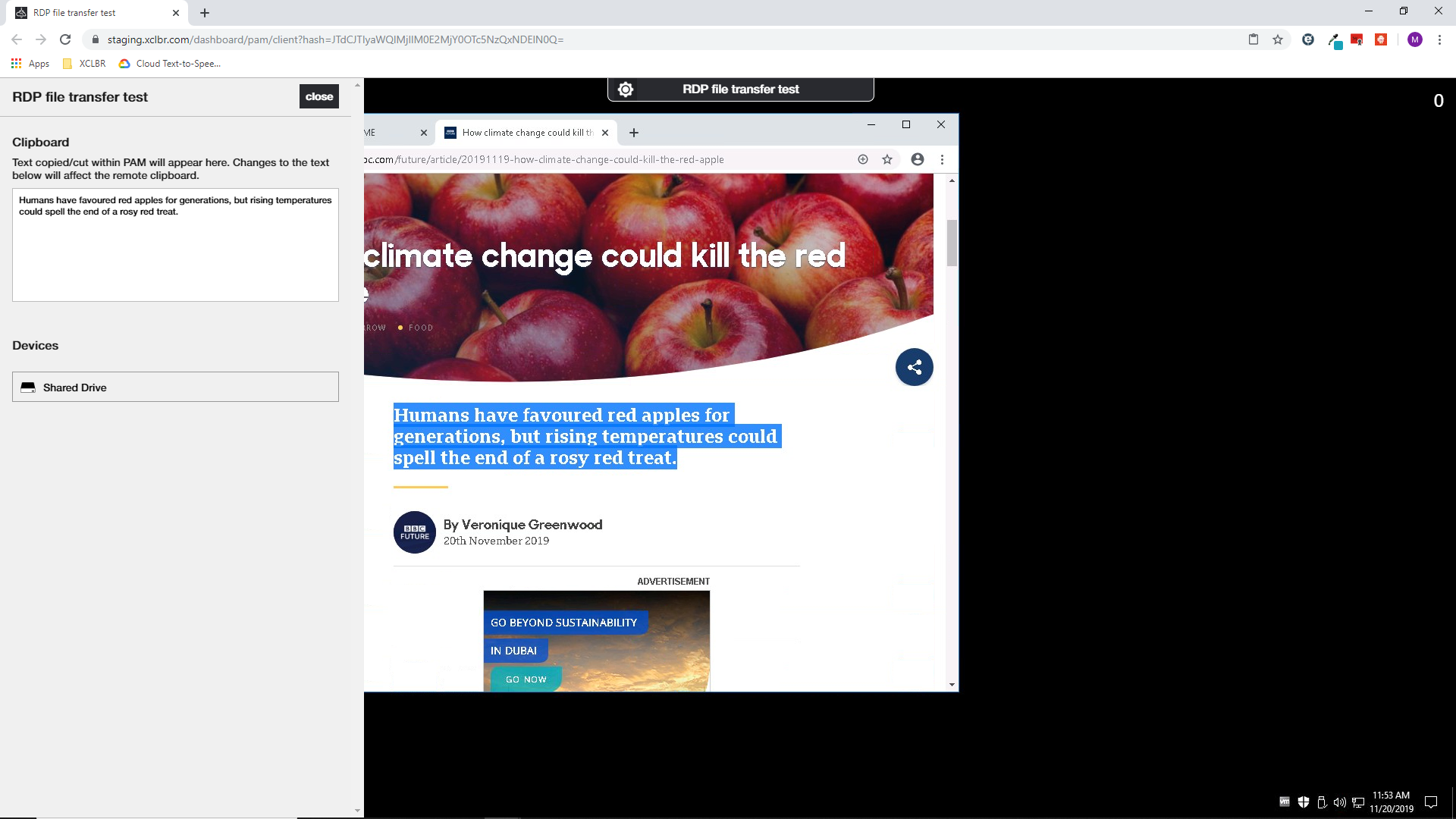
How to use clipboard (RDP)¶
Some browsers /FF etc/ do not support to use the shortcuts for straight copying text via browser to the target. Due to this fact, the PAM has integrated Clipboard from where it is possible to copy required text. If you wish to copy text to the target, select required text, click on the setting button at the top of the target screen and copy paste it to the Clipboard. Close the left panel with Clipboard and right click on required place on target to paste text. To copy text from the target, select text and right click on it. Choose copy or cut and click on the setting button at the top of the target screen. The selected text is located in Clipboard from where it is possible to copy it to the PC /on SSH target the text is copyied by selecting text/.
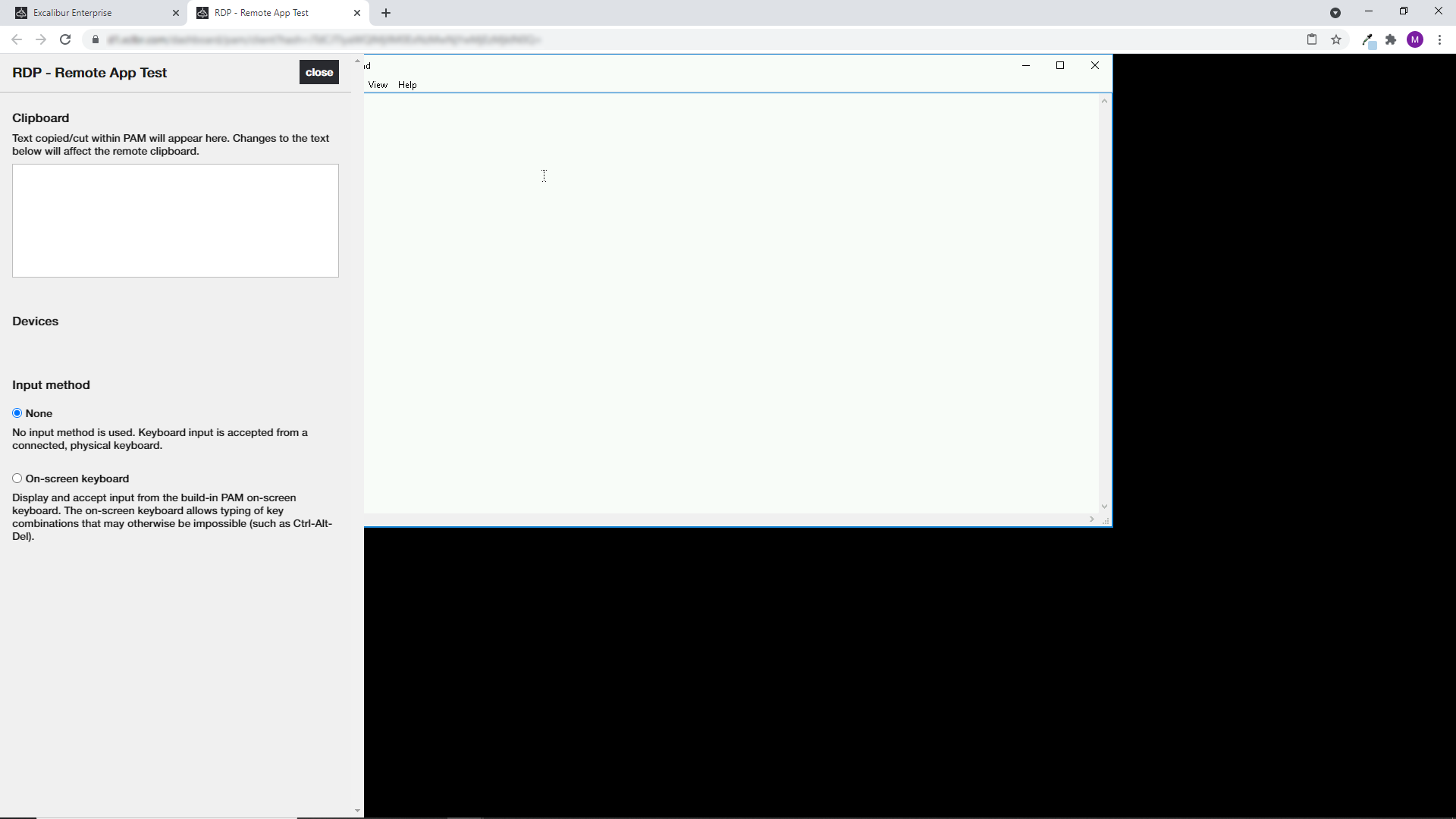
How to use a Virtual keyboard¶
In some cases is not possible to use a straight shortcuts from the user's keyboard. Due this fact Excalibur allows to use a virtual keyboard by which is possible to insert a shortcuts such as CTR+ALT+DEL, ALT+TAB etc. To activate a Virtual keyboard, open the session settings and click on On-screen keyboard and Virtual keyboard shows up. Close the session settings. By clicking on required combination of keys you are able to insert a shortcut. Yellow lightened keys mean that keys are holded and user can insert alphanumerical keys from virtual or own keyboard. Virtual keyboard allows to switch to another keyboard language. To change keyboard language, click on the selector located in the right top corner of virtual keyboard.
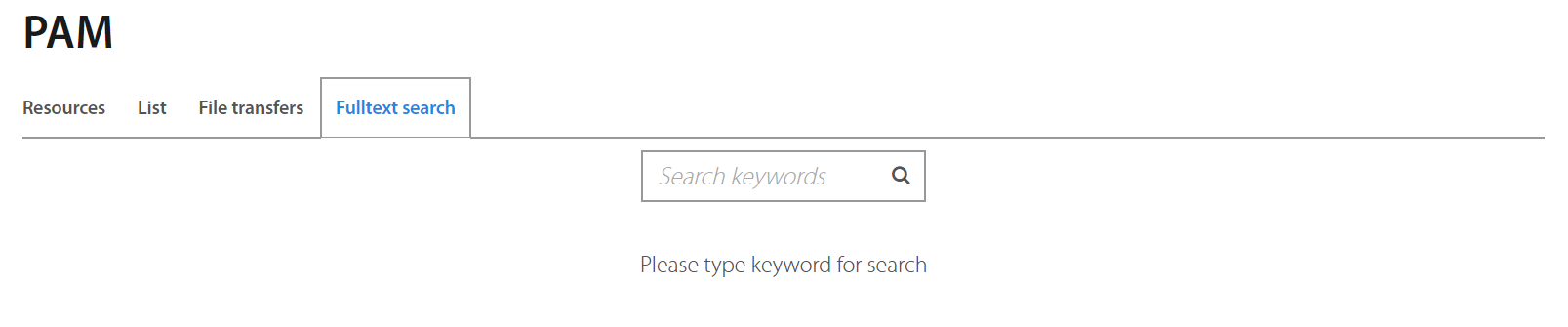
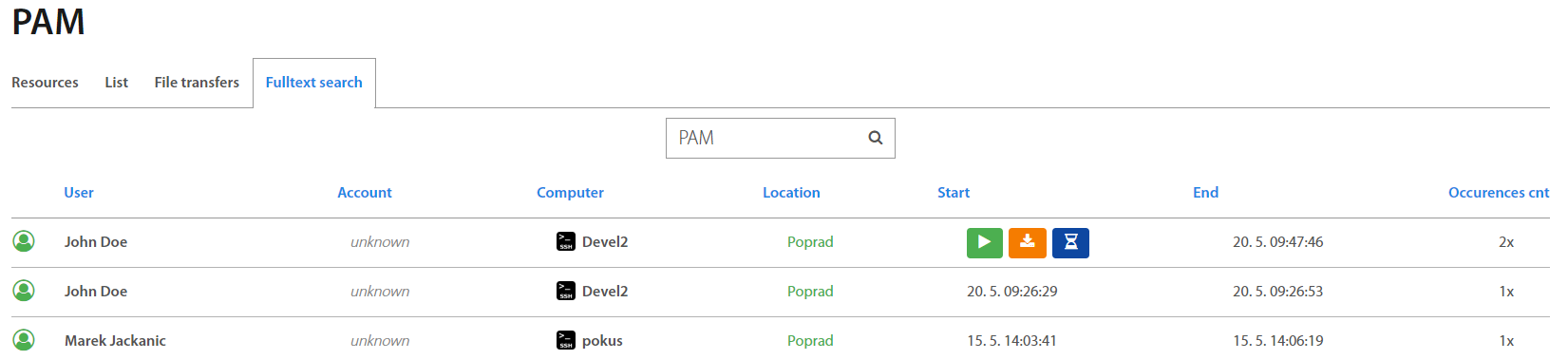
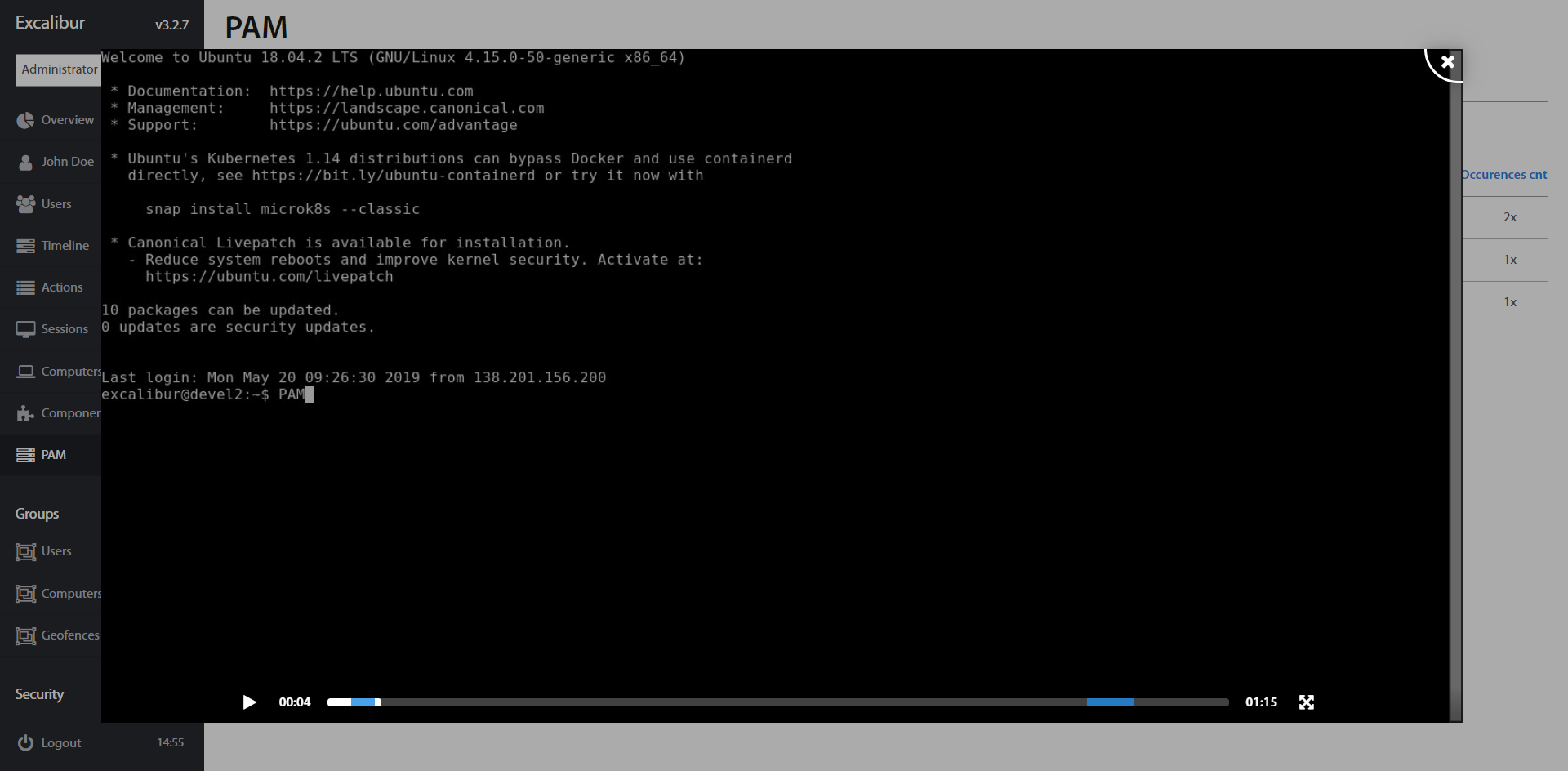
How to search word in performed session¶
Excalibur PAM allows you to find a full word which is inserted by the user during the PAM session. Each role has presetted rules of searching. Administrators, Service desks and Auditors can search words in all PAM sessions, managers can search in their own and subordinate’s PAM sessions. Users can search in their own sessions only.
Switch to Fulltext search tab and type the required word to search bar. Sessions with required word are shown immediately. The shown sessions consist of the user’s name who performed the session; Account; Computer which describes used PAM application; Location from where the session is performed, start/end date and time, and occurrence of the word in PAM session. By clicking on a specific item, further information is shown.
All sessions are recorded in real time and Excalibur allows you to define specific keywords which can detect the user’s potentially dangerous behavior and trigger defined automatic actions such as email notification and / or session termination.
Hover by mouse cursor over the required session and click on the button, to play the required session. Blue highlighted interval on the timeline is the place of the required keyword you search.
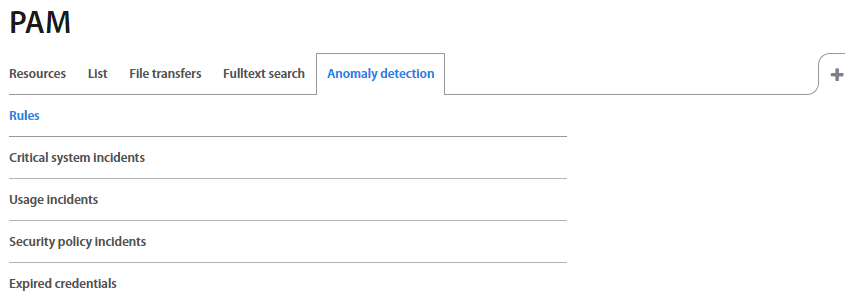
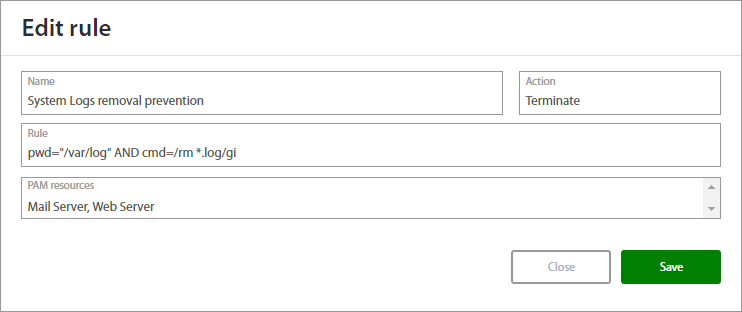
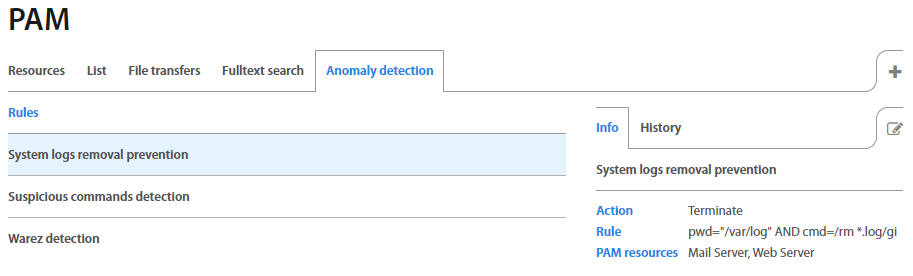
Anomaly detection¶
Excalibur PAM is able to monitor the user input and terminate the session when the system detects potentially dangerous behavior. Administrator can define the action - what happens with session such as termination and/or notification etc,
To add a rule for detection, click on the + button and define the fields:
| Field | Description |
|---|---|
| Name | Name of the rule. |
| Action | Terminate, Incident, Notice |
| Rule | Type the rules which will be detected. For example: pwd=/var/log AND cmd=rm. |
| PAM resource | ASelect PAM resources to apply rules for detection. |
To show detail of the rule, click on the specific rule and detail shows up. History tab shows a list of detected incidents.
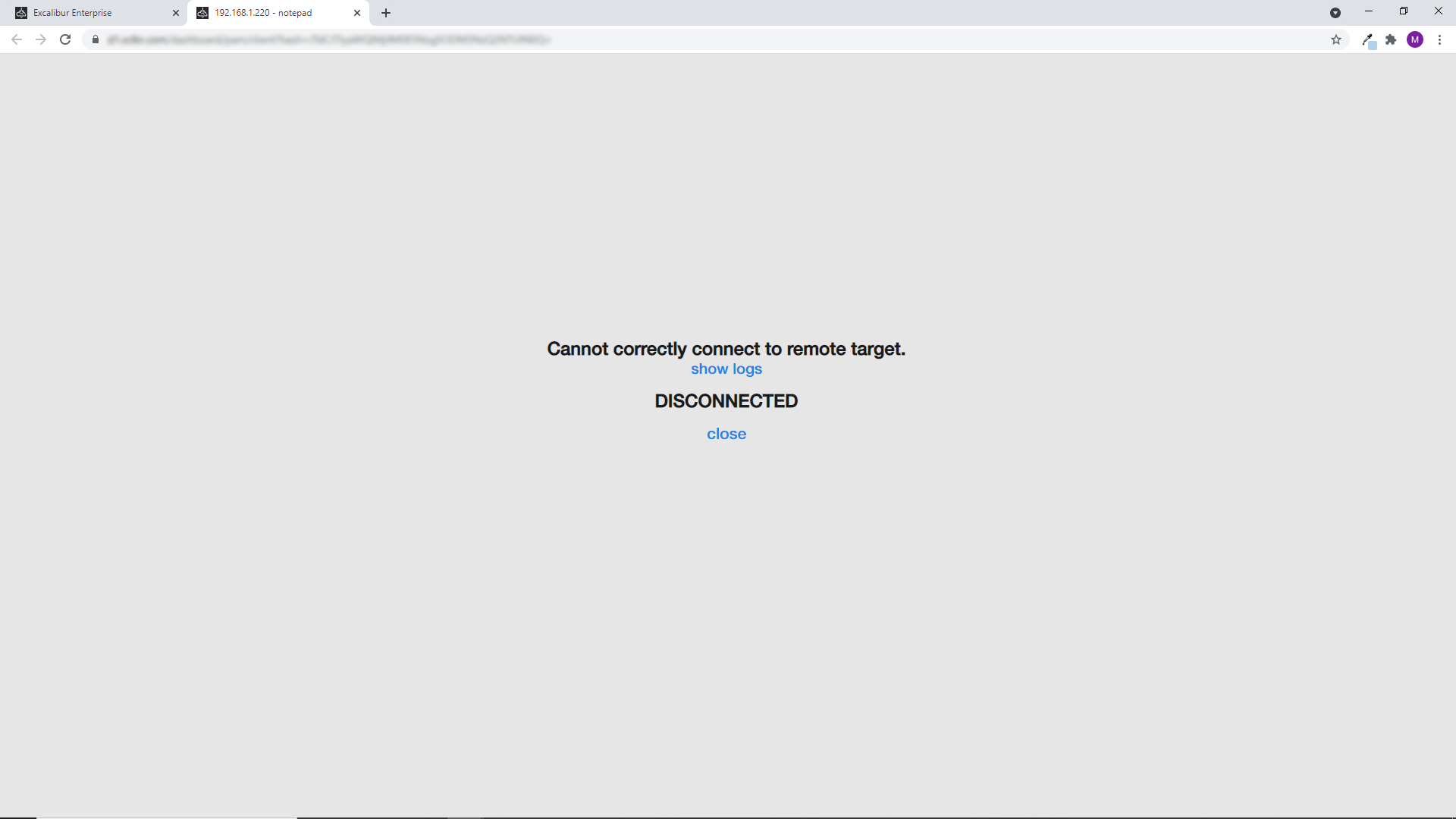
How to get logs from the PAM session¶
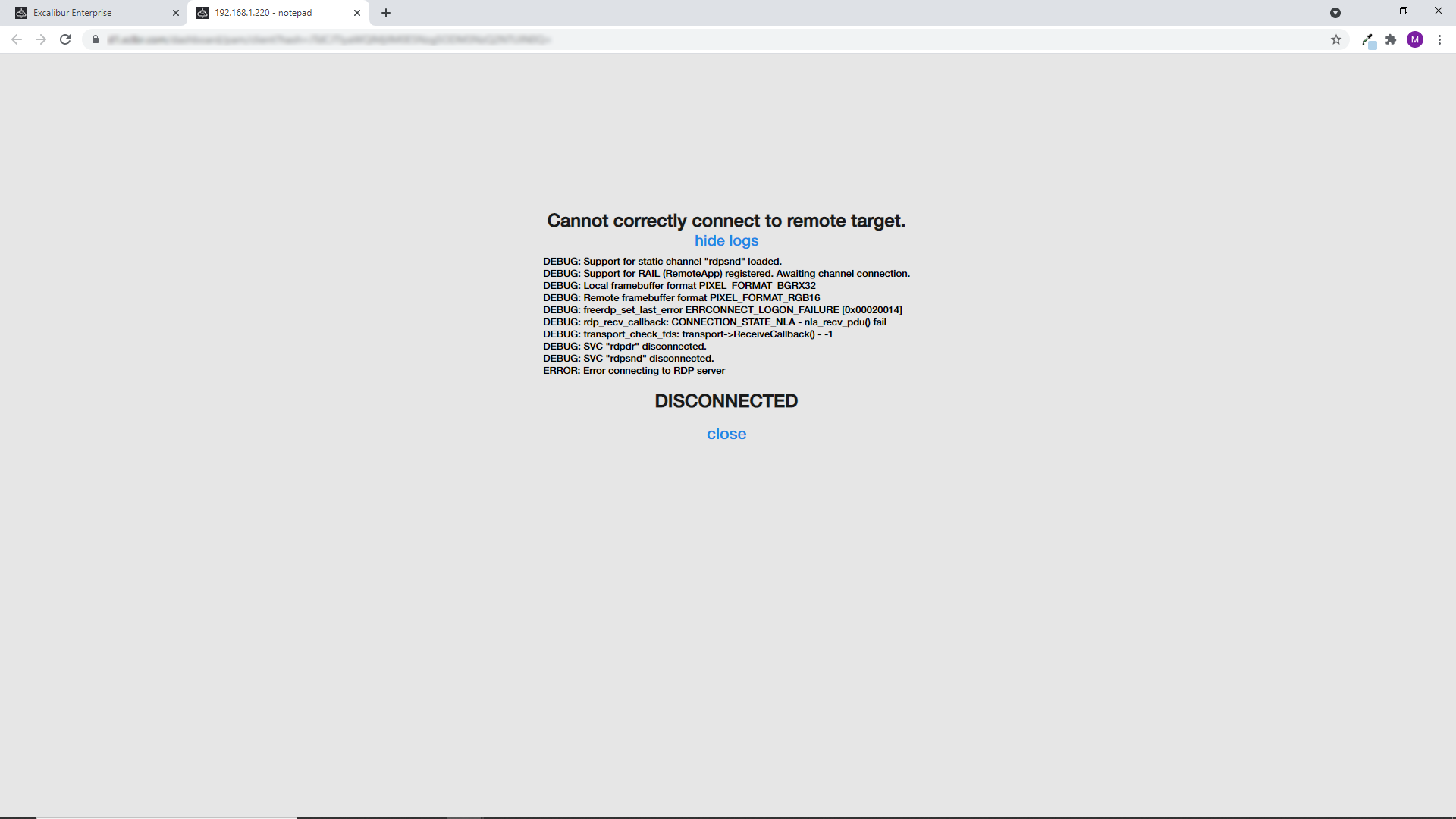
When PAM resource setup is incorrect or anything happens with the connection, then you are informed on PAM tab. To show logs click on Show logs.
RDP proxy connection¶
The native Remote client can be used for Excalibur PAM RDP proxy connection, which provides text clipboard and file transfer drive / folder sharing. All proxy sessions are recorded by default.
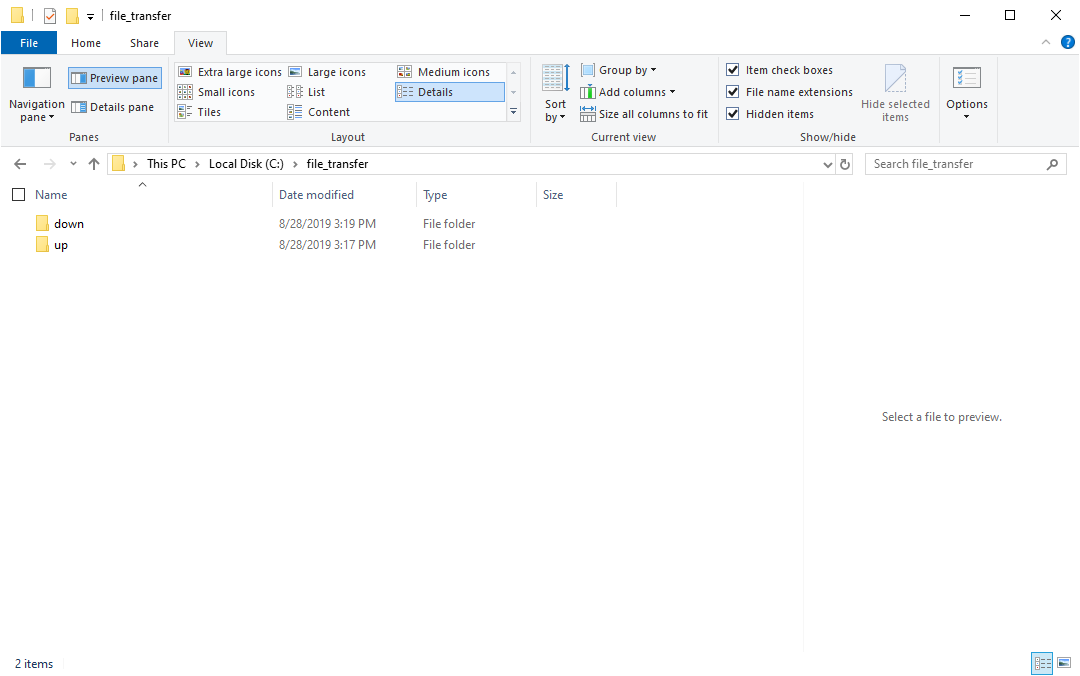
How to enable file transfer via RDP proxy¶
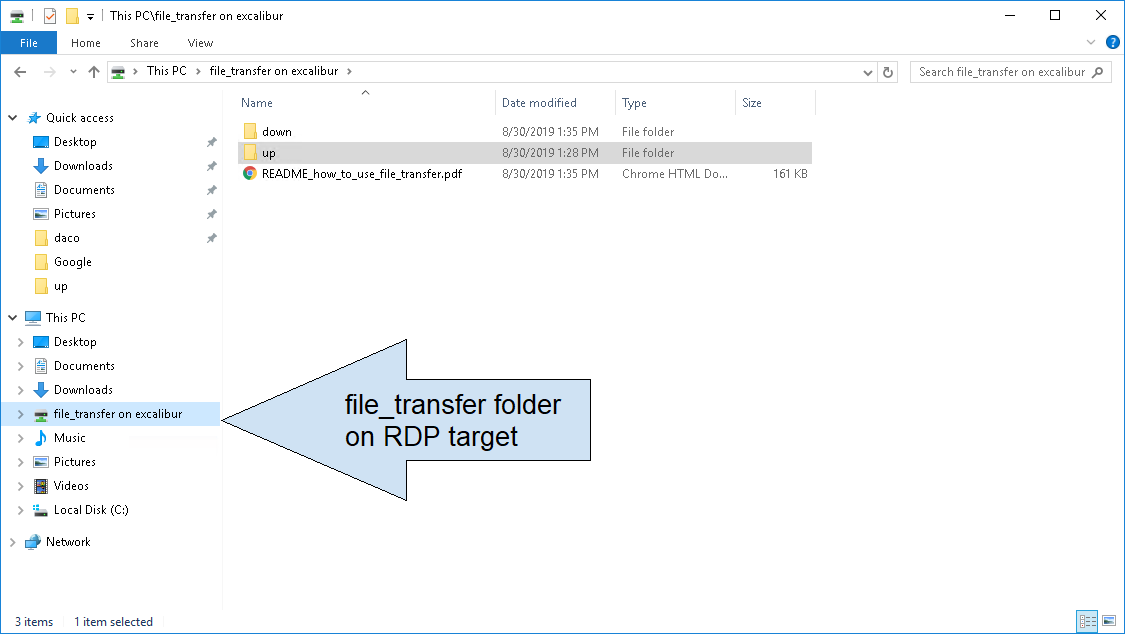
Create a folder named file_transfer in the drive / folder that you are sharing via RDP/. In this folder the subfolder “Down” should be automatically created when the RDP session will be active. If you wish to upload files via RDP, create a subfolder named “Up”. Everything in the subfolder “Up” will be synchronized from the RDP client to the RDP target. Everything in the subfolder “Down” will be synchronized from the RDP target to the RDP client
The following step is to enable local devices and interfaces in the Remote client. Make sure printers are NOT shared, else file transfer will not work
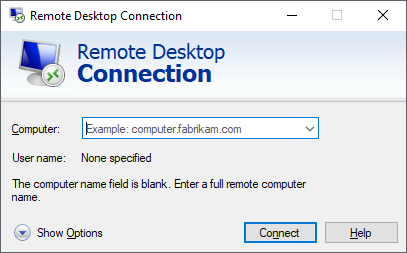
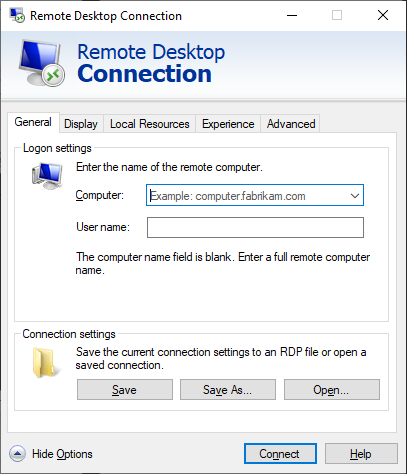
Click on "Show Options"
Switch to "Local Resources" tab
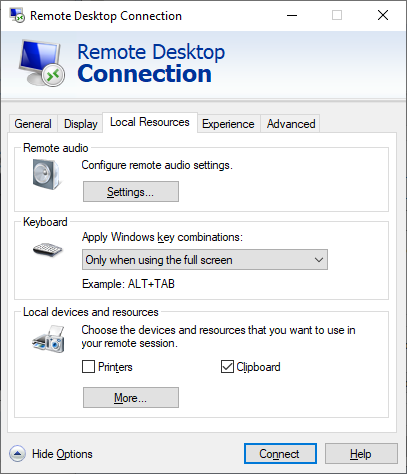
Uncheck "Printers" and check "Clipboard". Click on "More" button.
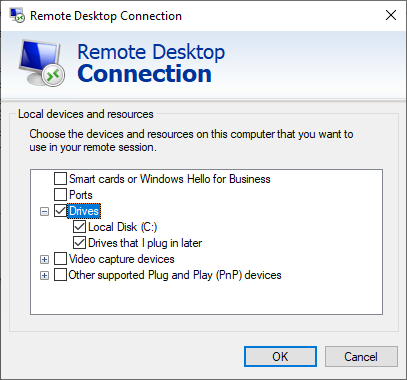
Select "Drivers"
Login with PAM RDP proxy¶
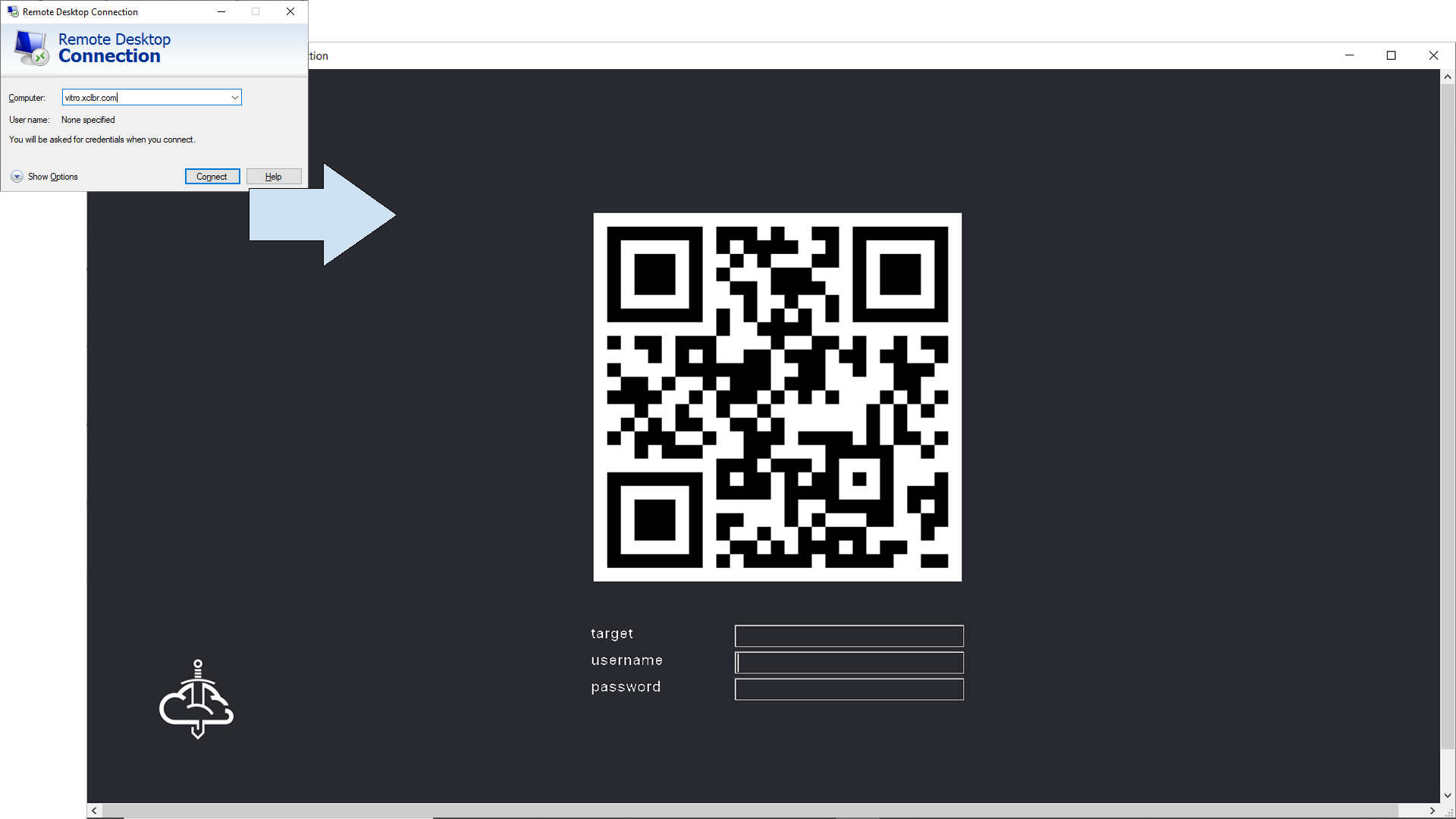
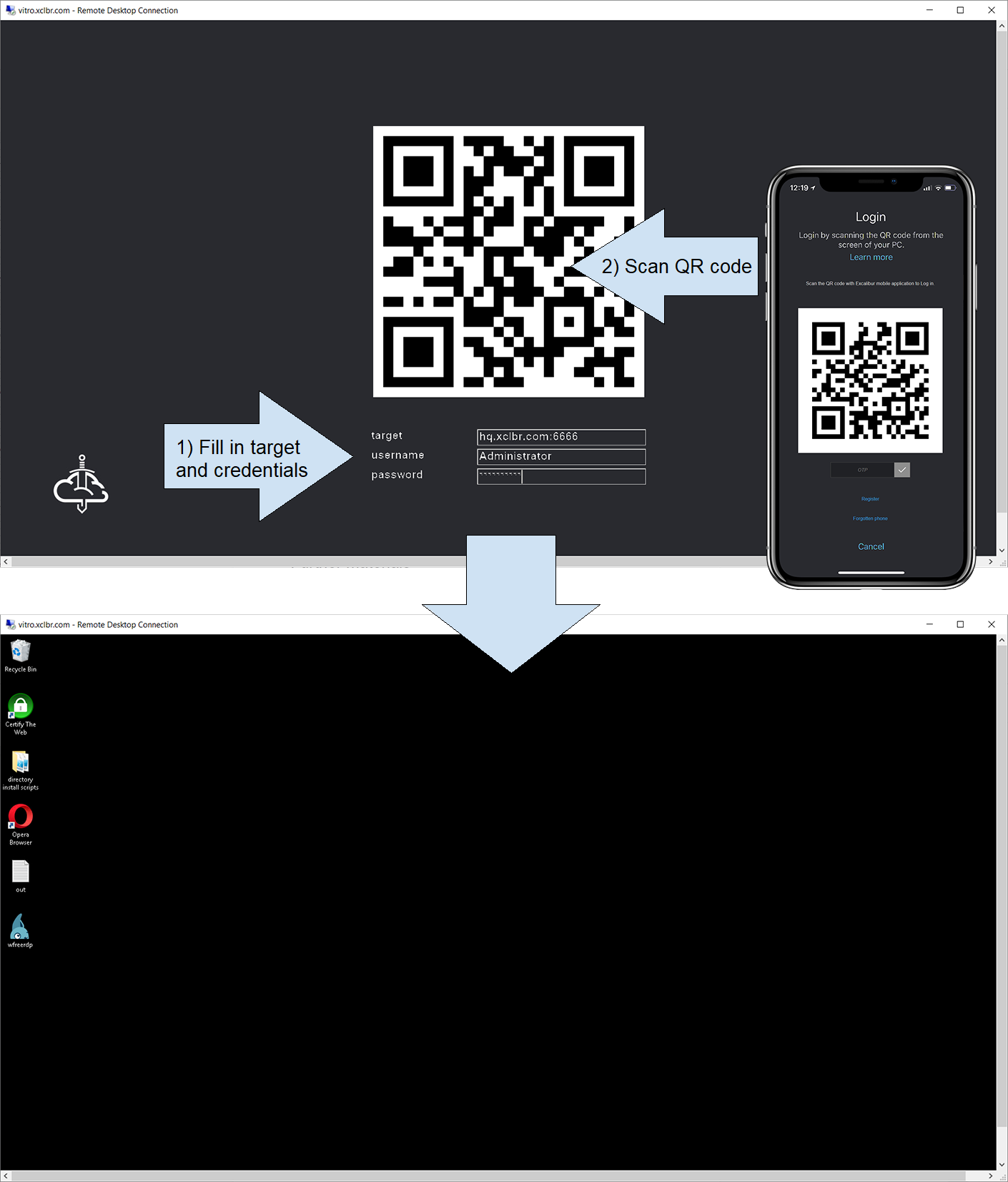
As is described in the previous chapter, the native Remote client can be used for connection to Excalibur PAM RDP proxy. Fill in the address of the host where the client will be connected, click on the Connect button and Excalibur PAM RDP proxy window is shown.
Fill in the address of the required target and credentials to access to target and confirm connection by scanning QR code. Now, you should be connected to the target.
File transfer and Clipboard¶
As is described in the previous chapter, everything in the subfolder “Up” will be synchronized from the RDP client to the RDP target. Everything in the subfolder “Down” will be synchronized from the RDP target to the RDP client. The file_transfer folder on RDP target is localized as a shareable device.
Excalibur PAM allows use the keyboard shortcuts (CTRL+C, CTRL+X, CTRL+V) to transfer text between RDP client and RDP target.
Further materials¶
Excalibur User Dashboard Manual