Excalibur v4
Enterprise-grade Streamed Access Management with Zero Trust Architecture
Platform Features
Comprehensive privileged access management built on Zero Trust principles
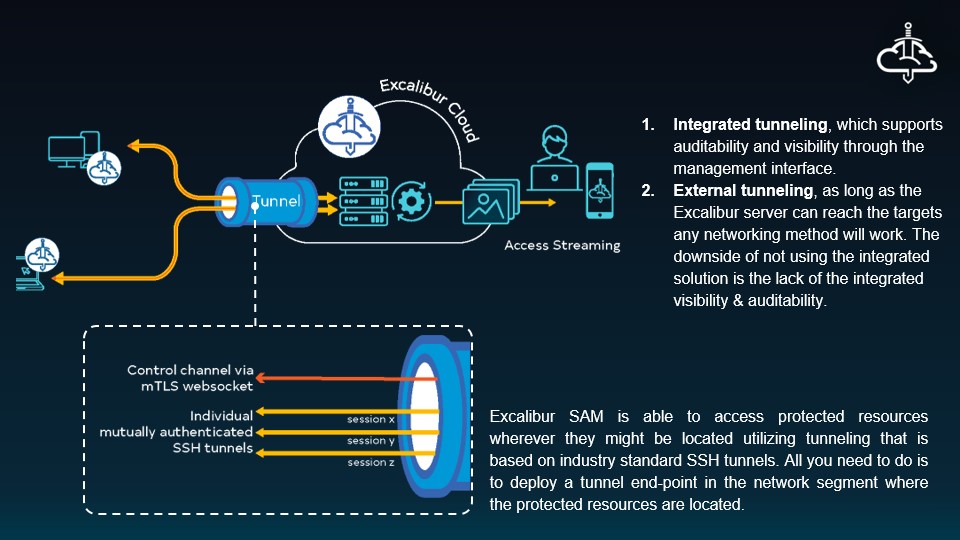
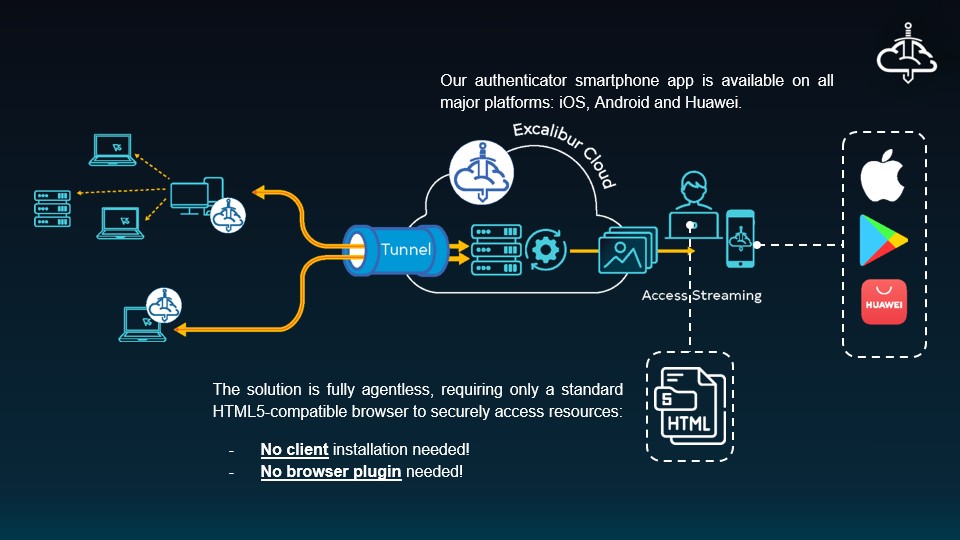
Secure Tunneling & Access
Industry-standard SSH tunneling with integrated visibility and complete audit trails.
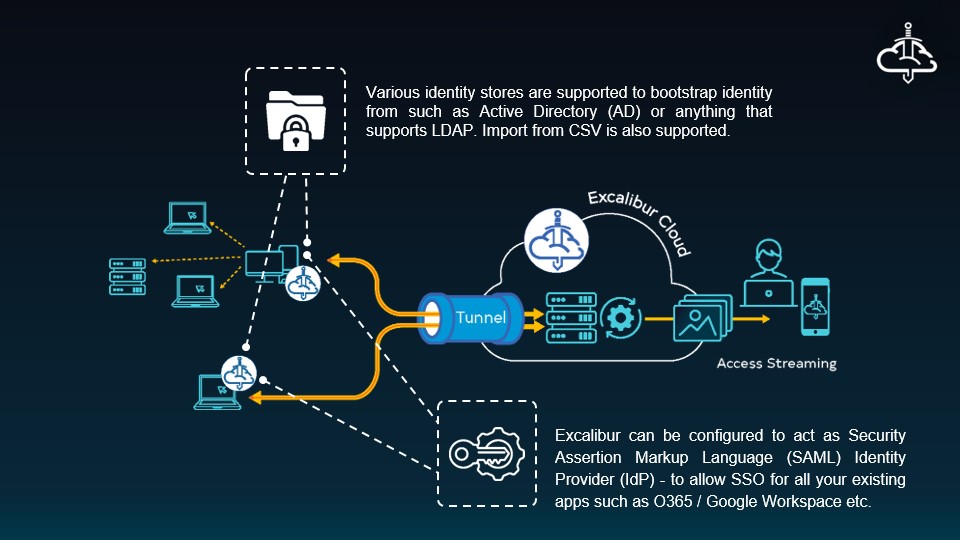
Identity Management
Seamless integration with Active Directory, LDAP, SAML, and cloud identity providers.
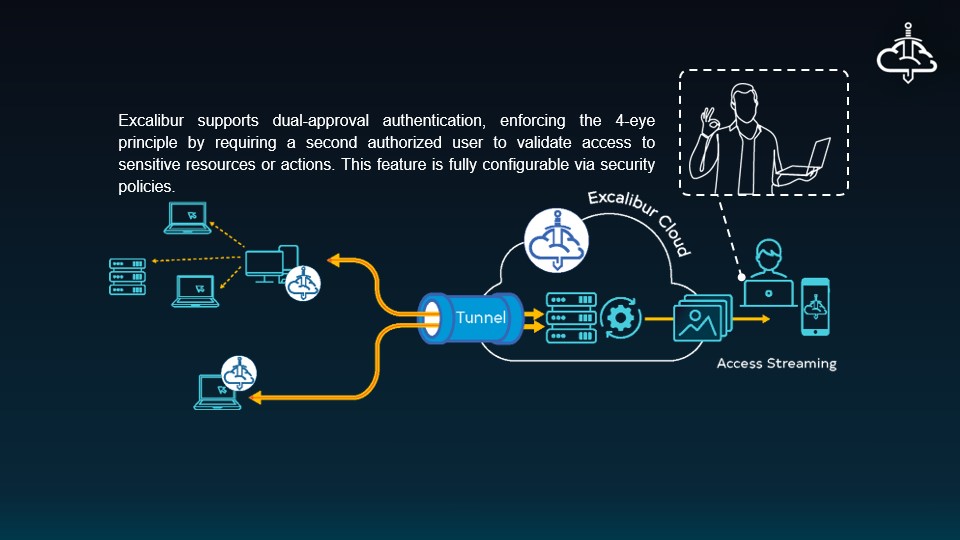
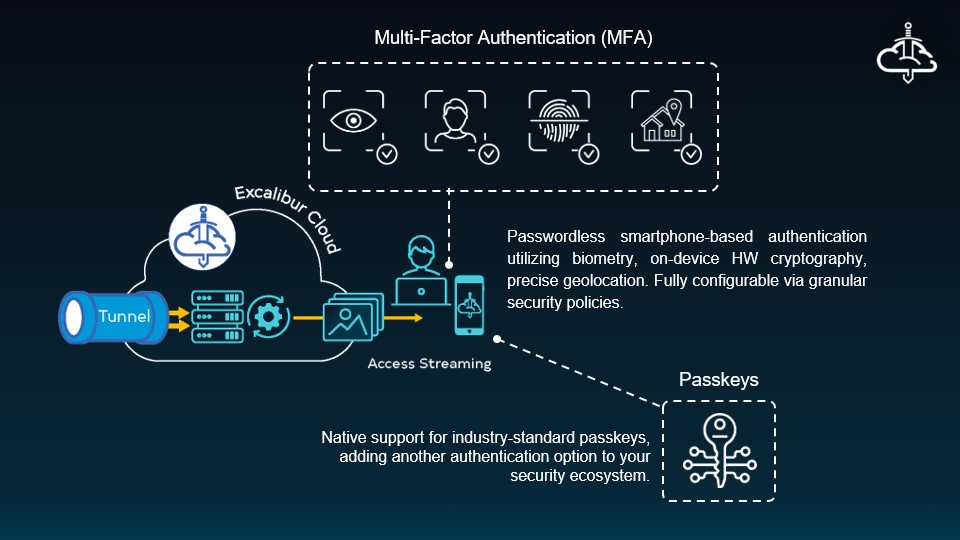
Advanced Authentication
Passwordless MFA with biometrics, passkeys, hardware keys, and 4-eye principle enforcement.
Protocol Support
SSH, RDP, VNC, and web target streaming with proprietary VITRO technology.
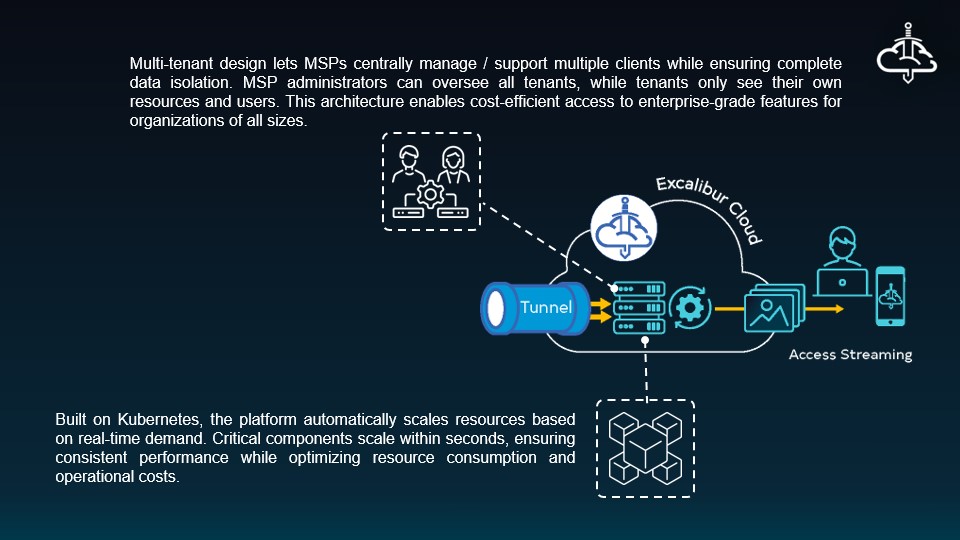
Cloud-Native Architecture
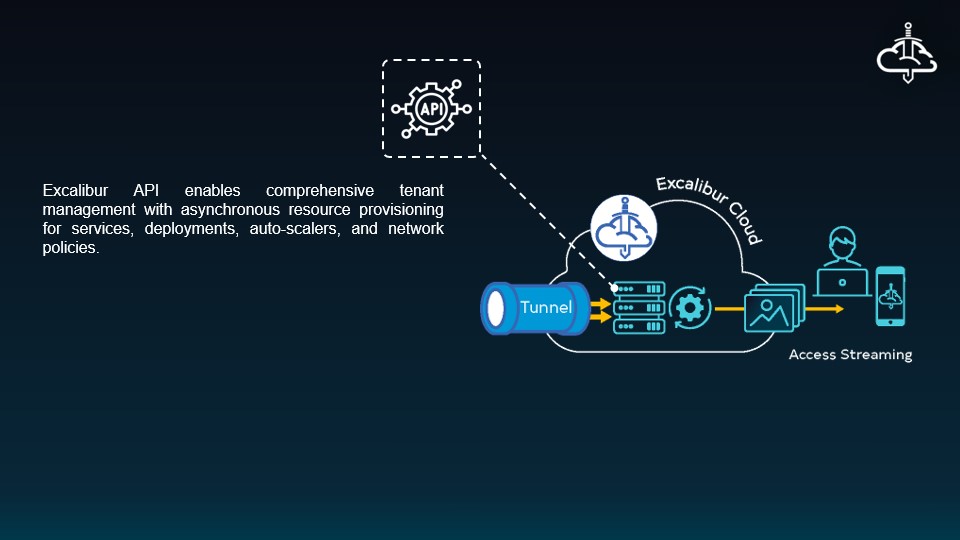
Kubernetes-based platform with auto-scaling, multi-tenant isolation, and MSP readiness.
Monitoring & Compliance
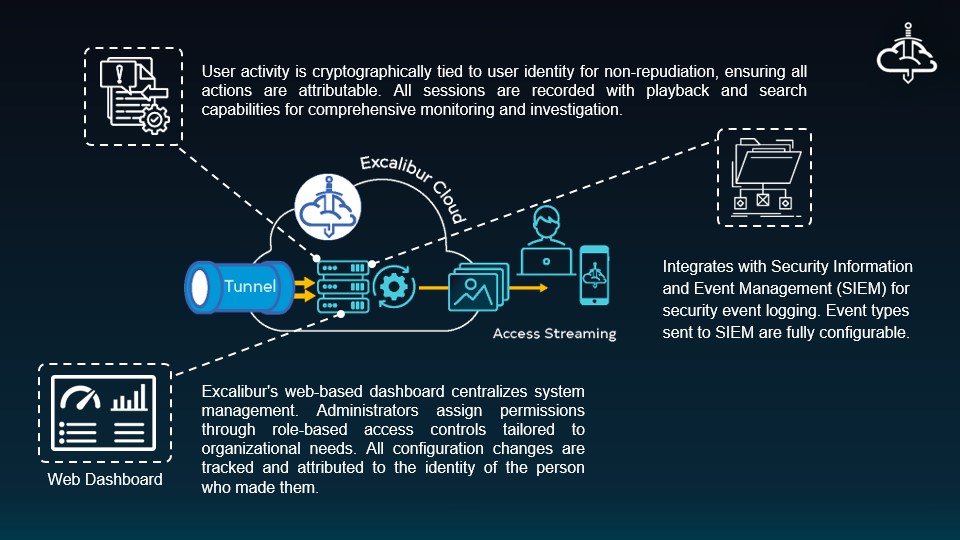
Full session recording and playback with SIEM integration and role-based access controls.
Architecture & Integration
See Excalibur in Action
A selection of short product walkthroughs — more videos coming soon covering additional targets, authentication flows, and admin workflows. Want to see a specific topic? Let us know.
Platform Capabilities
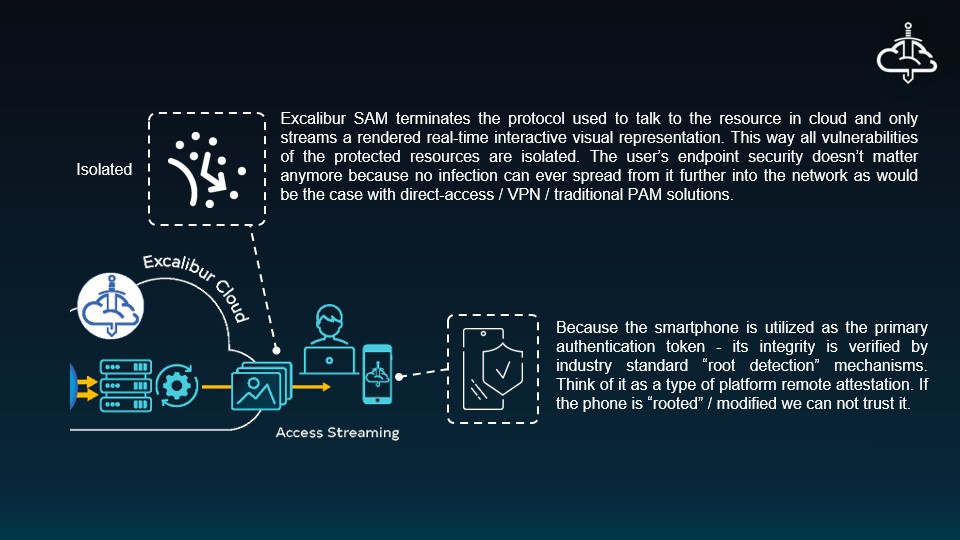
Streamed Access Management
Isolation and real-time AI security — stop attacks before they reach the app.
Just-in-Time (JIT) Access
Request, approve, revoke — ephemeral access with AI that enforces the approved intent.
Tunneled Target Access
Reach PAM targets through the Excalibur tunnel — no direct network exposure.
Machine Identity & Credential Mediation
Brokered machine identity — workloads hold a label, Excalibur swaps it for the real credential on the wire.
Getting Started
User Registration
Completing enrollment on your phone and desktop.
Token-Based Login
Signing in to a workstation with a one-time token.
Passkey Authentication
Passwordless sign-in with biometrics and passkeys.
Grant Target Access
How to grant a user access to a PAM target.
Database Targets
MSSQL
Privileged access to Microsoft SQL Server targets with session recording.
Oracle
Privileged access to Oracle Database targets with session recording.
PostgreSQL
Privileged access to PostgreSQL targets with session recording.
Excalibur s.r.o.
Hraničná 12
058 01 Poprad
Slovak Republic
Excalibur projects
Our projects are funded by the European Cybersecurity Competence Center (ECCC) and co-funded by the European Union.
Get in Touch
For questions, feedback, or suggestions about this documentation, please use our
Feedback formFor product demos, trials, partnership opportunities, or any other inquiries:
- General inquiries: xclbr@xclbr.com
- Technical support: support@xclbr.com
- Partnership inquiries: partners@xclbr.com